Your Compromise Is Confirmed: How Threat Actors Access Hotel Accounts on Booking.com
Updated March 21, 2023

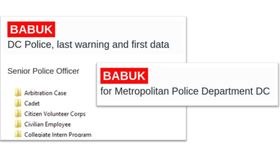
Over the last few months, several phishing campaigns were spotted using compromised credentials of hotels and homeowners. Particularly interesting is a widespread operation that employs these credentials to contact guests on Booking.com via their internal messenger (1, 2, 3, 4). In a fraudulent message, the attackers impersonate a hotel and lure victims into visiting a malicious phishing page designed to steal their credit card details.
How did the attackers get the credentials in the first place, to further abuse them? In several incidents, the compromised credentials are suspected to be obtained through information stealing malware targeting property owners. These info stealing campaigns appear to be targeted, impersonating a former hotel guest or following up on a reservation the attackers make. Once a property owner has clicked a malicious link, they get infected with an infostealer.
Researchers assume that both steps of such a campaign (first compromising the hotels and then contacting guests) are performed by the same actor or by different actors using the same manual. However, it is also possible that campaigns of this kind employ the cybercrime ecosystem to obtain compromised Booking.com credentials, since it provides a massive amount of data stolen by infostealers. KELA has analyzed the supply of such accounts in 2023.
Large Supply of Credentials for Booking.com Accounts
In 2023, KELA’s platform identified over 185,000 compromised accounts associated with Booking.com. What does this signify?
Over the past 12 years, KELA has been examining innovative and automated illicit markets on the cybercrime underground that sell access: login details, fingerprints, and additional data obtained from botnet-infected machines.These markets allow users to search for a resource, browse through a list of infected machines through which its credentials were stolen, and obtain the credentials alongside the user’s original web cookies.
KELA also monitors various sources on the cybercrime underground where dumps containing information stealers’ logs are offered for distribution and exchange. Once the stolen credentials (compromised accounts) are obtained by a threat actor, he gets access to the affected resources, such as Booking.com.
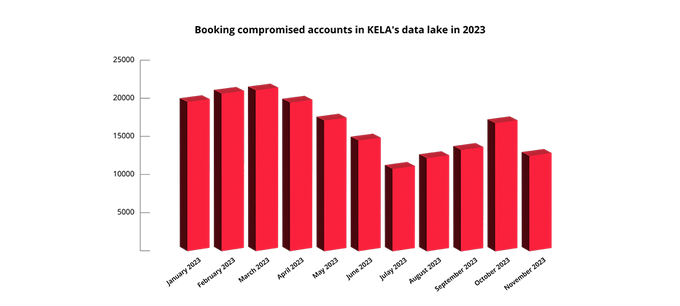
In 2023, each month of the year an average of 16,800 Booking.com compromised accounts were indexed in KELA’s data lake.
Property Owner Booking.com Accounts Offered for Sale Too
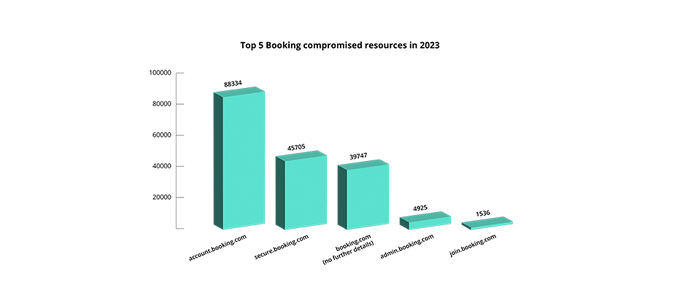
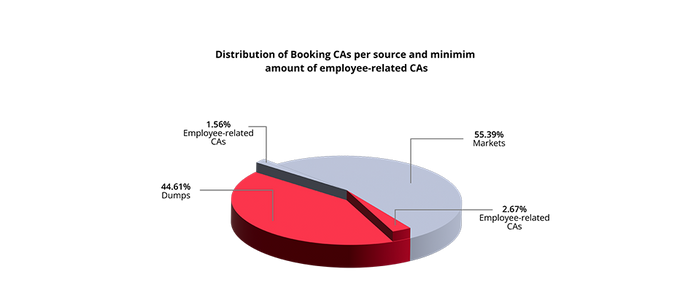
While we might assume that the compromised Booking.com accounts primarily belong to guests using the platform, a closer examination of the top affected subdomains reveals that the impact extends beyond guests. Infostealer infections have also affected employees of hotels and homeowners.
The top-3 resources, which account for around 93% of compromised resources, are general sign-in pages, which can be used by both guests and property owners. However, 3.5% are related to admin.booking.com (a subdomain for managing properties) and join.booking.com (a registration page for property owners). While the percentage appears low, there are actually almost 6,500 compromised credentials. This poses a significant risk, potentially enabling impersonation of thousands of properties on Booking.com.
But it doesn’t end here. Upon examining credentials exposed on general sign-in pages, KELA discovered hundreds of other corporate accounts, particularly those with property-related keywords in their emails. For example, if a stolen set of credentials contains an email address such as reservation@hotel*******.com, it is most likely associated with a hotel account.
And this is just a tip of the iceberg, since some hotels do not use indicative keywords in their credentials. In addition, this is something that can be examined only in stolen credentials originating from dumps (which allow viewing credentials right away. On the markets, in order to receive access to credentials, a threat actor has to buy information from each infected computer one by one.
Therefore, the actual amount of hotel-owned accounts that have been compromised through infostealers and are currently available for purchase on cybercrime underground, is potentially much higher than the numbers provided above, resulting in thousands of compromised accounts and providing threat actors abusing Booking.com with endless amounts of opportunities.
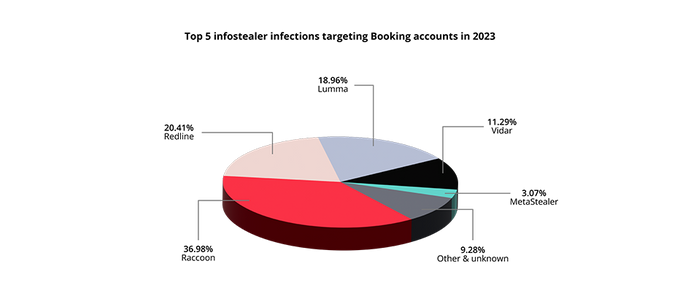
Threat Actors Just Love Targeting Properties
The most common infections used to steal accommodation accounts have been Raccoon, Redline, Lumma, Vidar and MetaStealer, all commodity infostealers available for purchase as malware-as-a-service. This means that after different actors had targeted properties using this malware whether in targeted or opportunistic campaigns, they decided to monetize it by selling. Consequently, this opened the door for numerous other cybercriminals to exploit the stolen access.
In addition to obtaining access from these sources, threat actors also seek to sell and buy private logs not available on markets and shared dumps. This significantly amplifies the pool of available Booking.com accounts for threat actors.
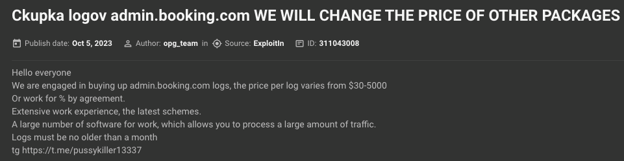
Threat actor ready to buy logs related to admin.booking.com (auto-translated through KELA platform)
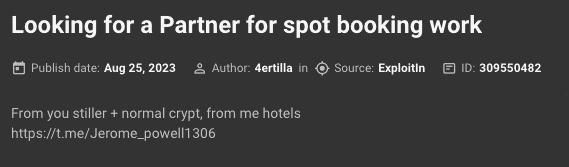
Threat actor seeking a partner with an infostealer to exploit hotels on Booking.com
How to Protect Your Organization
KELA assumes that the evolution of cybercrime, characterized by a shift towards servitization and sales automation, as well as increased visibility of goods, will motivate more threat actors to leverage this ecosystem. In particular, a well-established network for trading logs makes it easier for threat actors to gain access and scale their attacks. This supply chain will only grow stronger in light of the unfading popularity of information stealers offered as malware-as-a-service.
Fortunately, threat intelligence solutions such as KELA’s platform, provide organizations’ network security teams and threat intelligence practitioners with real-time insights into underground cybercrime activities that pose risks to the organization’s digital assets. These insights facilitate the efficient monitoring of exposed assets, including company SAAS accounts, and contribute to reducing the attack surface through prompt exposure remediation or the removal of compromised data.
We recommend monitoring not just “classic” network assets like domains and IP ranges, but also unique URLs and identifiers used on external cloud services, for instance organizations’ unique Slack URLs.