GDPR Gambit: The New Favorite of Ransomware and Extortion Actors?
Published September 6, 2023

“I wonder what the GDPR agency will think about our relationship?” — approaches one of its victims on their blog RansomedVC, a relatively new extortion collective that emerged in August 2023. The word has quickly spread that this actor is leveraging GDPR (General Data Protection Regulation), a tactic that has never been observed before. However, many attackers have been using GDPR threats in their ransom notes and blogs to pressure European victims into paying them, similar to RansomedVC. In this blog, KELA looks at actors using GDPR as their leverage.
Threats to release data and face GDPR fines have been exploited by ransomware & extortion actors for the last few years. For example, now-defunct Suncrypt in their ransom notes addressed their victims: “GDPR. Don’t want to pay to us, pay 10x more to the government.” Another gang, Grief, referenced specific paragraphs of GDPR: “GDPR at Article 33 requires that, in the event of a personal data breach, data controllers should notify the appropriate supervisory authority.” While these ransomware actors are long gone, the trick is still in the books.
Looking at 2023, we see that several ransomware & extortion actors just like to mention GDPR in their blog posts, with Alphv (BlackСat) and NoEscape leading the list.
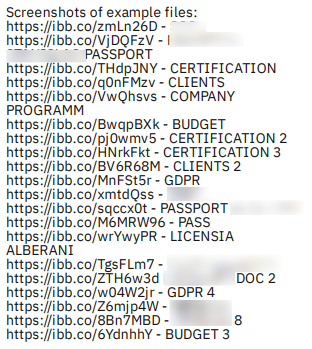
For Alphv, the US is still undoubtedly their favorite target: in the last year, they have publicly claimed around 200 US victims, while Europe is in second place, with only (in comparison) 65 European victims. Alphv has been mentioning GDPR in their blog posts since 2022, in most of the cases highlighting GDPR-related files in the leaked data:
Alphv publishing proof files for an attack on a fruit and vegetable supplier in Italy in January 2023
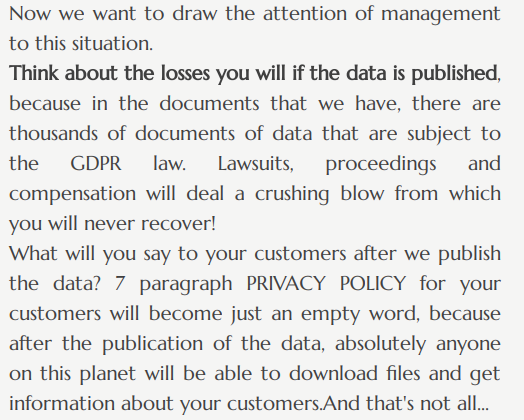
NoEscape, a ransomware group that emerged in 2023, doesn’t have a lot of disclosed victims so far, but in 42 victims they published, European companies are leading (contrary to the year trend of all ransomware & extortion attacks, where US companies are attacked the most). Making threats related to GDPR, NoEscape uses what can be called a personal approach.
For example, when posting about a UK-based technology company in August, they claimed: “Do you understand what damage will be done to your company if we just get the contact list of your clients and make a mailing list with a notification that all the data that they stored on your servers has been compromised and will be publicly available through the fault of your company? OH YES, you perfectly understand what the consequences will be because you hosted a webinar in 2018 whose topic was the General Data Protection Regulation (GDPR).”
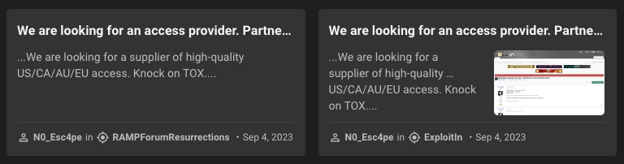
The gang’s representatives on cybercrime forums are regularly looking for Initial Access Brokers to supply them with access to companies from the US, Canada, Australia and Europe.
NoEscape threatens an Italy-based jewelry company in August 2023
Recent NoEscape’s posts meant to find an access supplier as seen on the KELA platform
Among new extortion groups that adopted the same tactic is Cloak, an extortion actor that has been linked to the Good Day ransomware operation. Half of the victims on a recently emerged Cloak’s blog are located in Europe. In their ransom notes, a pretty standard phrasing is used for the victims, specifically appealing to GDPR. Based on this fact, it seems that the group could be focusing on attacking European victims, otherwise the threat would not be included in their ransom notes template.
A ransom note of GoodDay, which provides credentials for a negotiation site, where the actors threatened to release data on Cloak
While other countries have their own data protection laws in place, KELA did not find evidence that they are extensively used by ransomware & extortion actors to pressure their victims into paying ransom. GDPR threats, on the contrary, seem to be used by different attackers over time. Depending on the success of these attempts, it is possible that more actors will adopt the tactic and will attack European victims more.
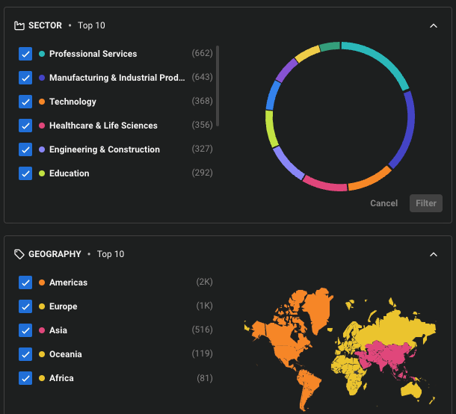
Currently, the US alone is still attacked more than European companies: in the past year, it’s almost 2000 US victims against around 1000 European victims.
Top attacked sectors and countries for the past year as seen on KELA’s platform
Get notified about threats targeting your organization in real-time. Try KELA’s Cyber Threat Intelligence Platform for Free.