TPRM
KELA’s intelligence-driven Third-Party Risk Management (TPRM) module is a cutting-edge security solutions designed to monitor, evaluate, and mitigate risks from third-party vendors within your supply chain.
This module is essential for organizations looking to enhance their cybersecurity posture against external threats.

KEY FEATURES

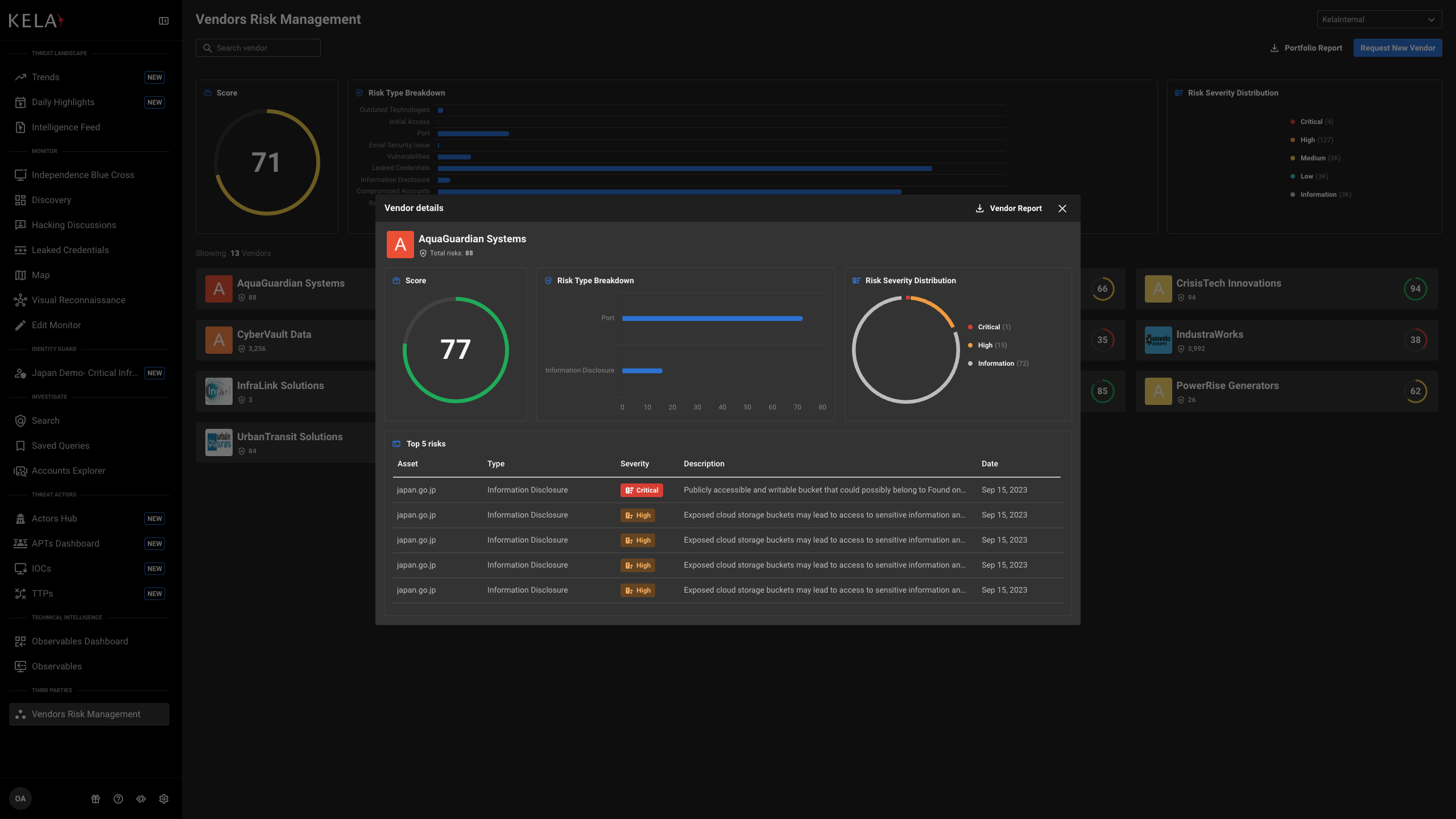
Third-Party Attack Surface Monitoring
Comprehensive vendor asset discovery, integrates relevant intelligence findings, and continuously monitors potential threats on both known and unknown vulnerabilities. This enables a detailed analysis , from an overall risk score down to actionable raw data, providing insights as seen through the eyes of the attacker.

Predictive Risk Scoring
Modeled and trained with intelligence on thousands of validated cyber incidents, KELA’s predictive risk score allows you to stay ahead of potential threats and take action before an attack occurs.

Prioritized Risks for Remediation
Automatically prioritizes the top risks for remediation per each monitored vendor along with associated threat intelligence and recommended corrective measures.

Automated Risk Reports
Includes high level and in-depth information about intelligence collected by KELA. These reports can be used to share information with third-parties and support prioritization and remediation processes.
Proprietary Scoring Algorithm
KELA’s predictive scoring algorithm synthesizes validated data on current and impending threats from KELA’s comprehensive cyber threat intelligence and attack surface monitoring solutions, enabling dynamic risk scoring that adjusts as new information surfaces.
Benefits
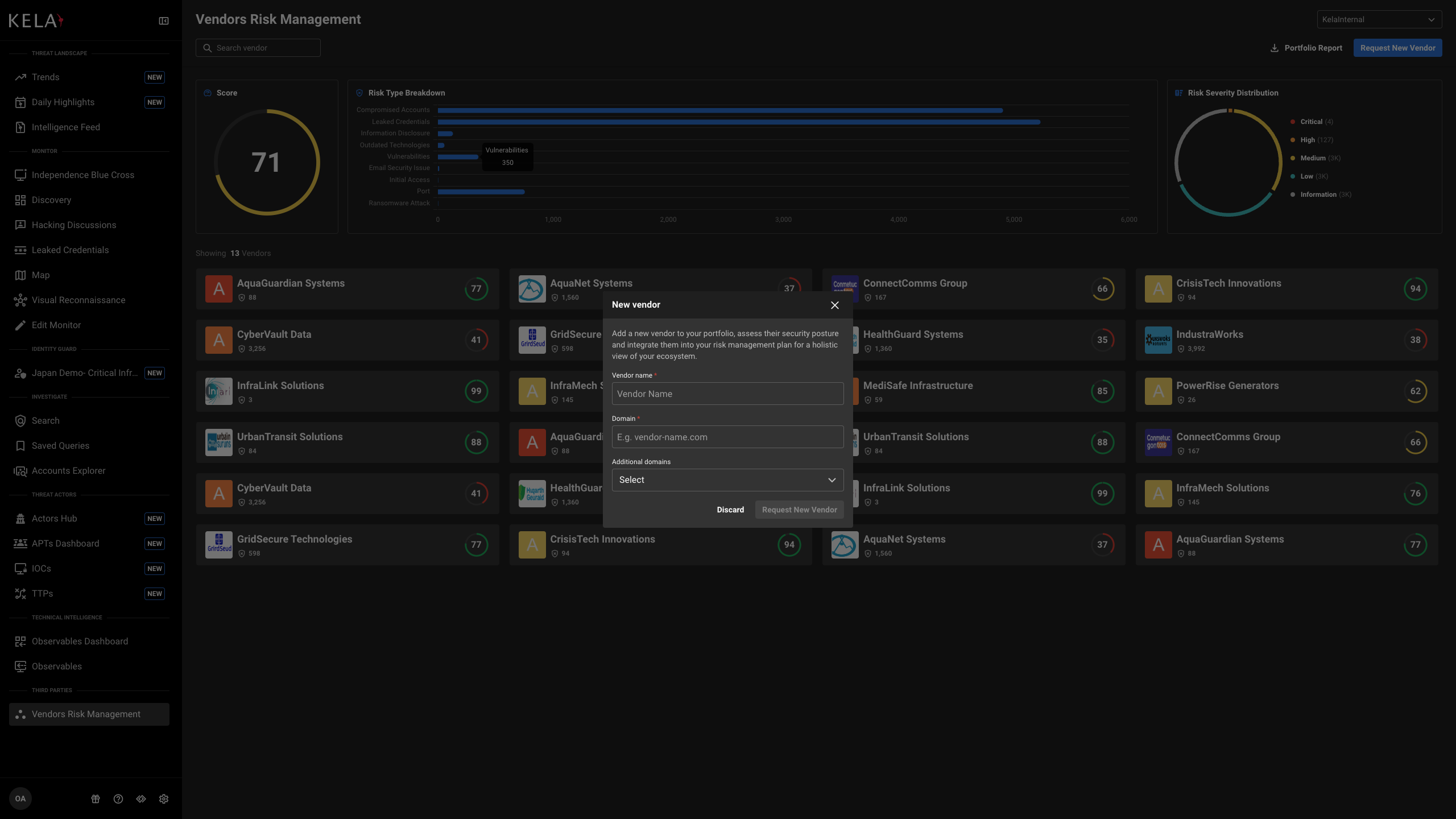
Frictionless Vendor On-boarding
Scale up and easily on-board third-party vendors without the need for lengthy questionnaires and
consent forms. With KELA's permission-less monitoring approach you gain immediate and actionable
insights on your vendors’ security posture.
Proactive Risk Management and Remediation
Forecast threats and prioritize responses with KELA's predictive risk scoring. Automatically identify
critical vulnerabilities, with actionable insights to enhance remediation efforts
Operational Efficiency and Collaboration
Speed up collaboration and effectively support third-party remediation efforts with informed decision making and improved communications.
Technical Approach
Assets Discovery
Identifies and catalogs digital assets associated with third-party vendors during the onboarding process.
Risks Collection
Gathers and analyzes data from various categories, including Threat Intelligence Exposure, Attack Surface Management, and Technical Intelligence.
Score Calculation
Analyzes collected risk data using a proprietary algorithm to accurately calculate and assign risk scores to each vendor.
Portfolio Analysis
Provides an overview of all vendor relationships, highlighting trends and distributing risk insights to facilitate strategic decision-making.
Actionable Output
Generates automated reports with actionable insights for smooth collaboration and remediation.
Assets Discovery
Identifies and catalogs digital assets associated with third-party vendors during the onboarding process.
Risks Collection
Gathers and analyzes data from various categories, including Threat Intelligence Exposure, Attack Surface Management, and Technical Intelligence.
Score Calculation
Analyzes collected risk data using a proprietary algorithm to accurately calculate and assign risk scores to each vendor.
Portfolio Analysis
Provides an overview of all vendor relationships, highlighting trends and distributing risk insights to facilitate strategic decision-making.
Provides an overview of all vendor relationships, highlighting trends and distributing risk insights to facilitate strategic decision-making.
Actionable Output
Generates automated reports with actionable insights for smooth collaboration and remediation.
Use Cases
Enterprise Risk Management
KELA’s advanced Third-Party Risk Management module is pivotal for industries like banking, insurance, IT, computer software, healthcare, finance, telecommunications, and aviation. It equips these sectors with critical tools to thoroughly assess and mitigate risks throughout their digital supply chains, enhancing their security postures and operational resilience.
National Security
Allows Government bodies and law enforcement agencies to evaluate risk levels across various sectors, including critical infrastructure and public services. It also helps CERT’s support local businesses by providing actionable corrective measures and guidance, bolstering national security measures and sectorial safety.
Regulatory Compliance
KELA’s TPRM module supports compliance with major regulations such as HIPPA, DORA, PCI DSS, SEC, NIS, NIS2, and GDPR, helping your organization uphold strict security and privacy standards.