A Glimpse into August 2023 Vulnerabilities Discussed by Cybercriminals
Published September 9, 2023

In August 2023, KELA encountered several critical vulnerabilities that raised significant interest within the cybercrime underground:
- CVE-2023-3519 (Citrix ADC and NetScaler Gateway)
- CVE-2023-27997 (Fortigate)
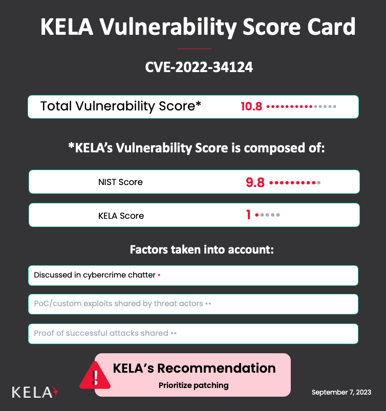
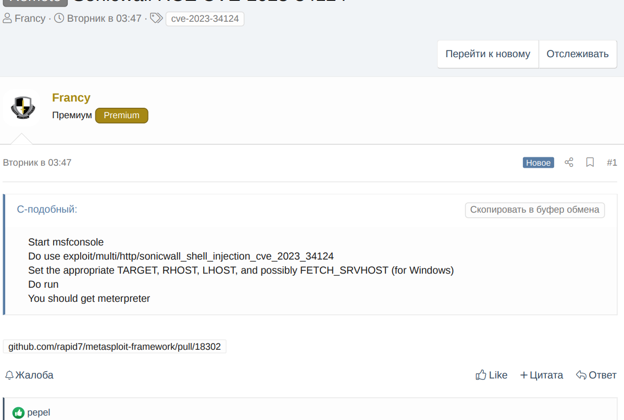
- CVE-2023-34124 (SonicWall)
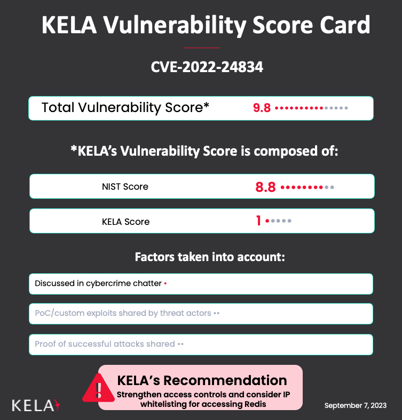
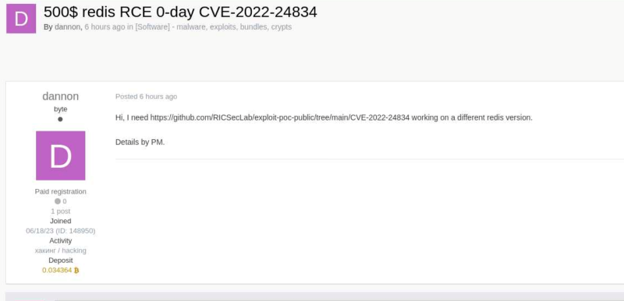
- CVE-2022-24834 (Redis)
This report highlights the details of each vulnerability, their implications, and recommendations for mitigation. In addition to known vulnerabilities, threat actors always look for buying 0-day vulnerabilities to exploit, and KELA highlights two recent cases related to flaws in Windows and TP-Link W8970 routers.
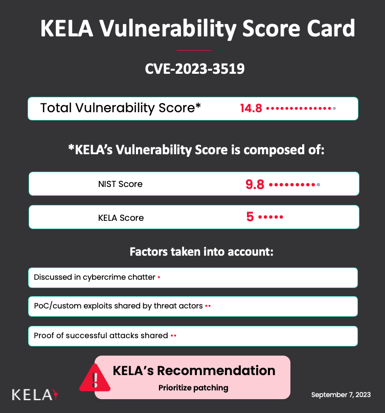
CVE-2023-3519 affecting Citrix ADC and NetScaler Gateway
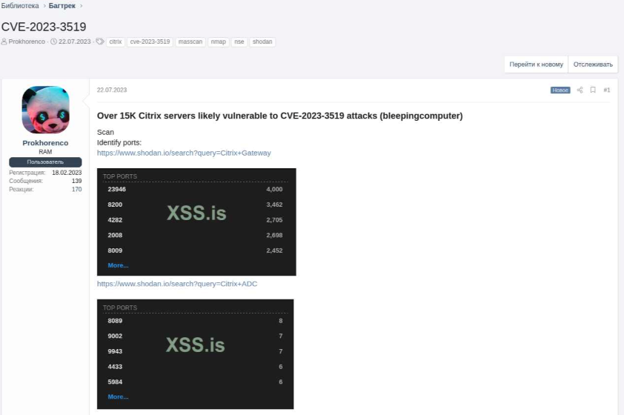
KELA observed discussions among cybercriminals regarding CVE-2023-3519, a vulnerability affecting Citrix ADC and NetScaler Gateway. This remote code execution vulnerability was disclosed in July 2023 and has been exploited in the wild since June as a zero-day to drop a webshell on a critical infrastructure organization’s non-production environment NetScaler ADC appliance. Since it was publicly disclosed, threat actors on cybercrime forums have been actively sharing tips on how to search for exposed servers using queries and code enabling them to find Citrix servers on Shodan and Masscan and check if they are vulnerable. When a PoC exploit was published on GitHub, it was immediately reshared in the cybercrime underground, implicating that threat actors can use already prepared lists of targets to exploit the flaw.
A beginning of a chatter discussing CVE-2023-3519
Users asking for exploits to CVE-2023-3519, and asking technical questions about citrix access related to the vulnerability
Meanwhile, in August, researchers continued to report about a mass-exploitation campaign, which was likely conducted by a threat actor, potentially linked to the FIN8 hacking group. The actor tracked as ‘STAC4663’ was seen exploiting the CVE-2023-3519 vulnerability to perform payload injections into processes like “wuauclt.exe” or “wmiprvse.exe”, deploy Blue VBS obfuscated PowerShell scripts and PHP webshells . Researchers suspect this to be part of a ransomware attack chain, possibly linked to the FIN8 group that has deployed the Alphv (BlackCat) ransomware previously.
Considering the vulnerability is being exploited both by organized groups and single actors active in cybercrime underground, it appears to cause significant threat for organizations. However, one of the actors noted on August 20 that most of the targets should have been exploited by now, especially considering the fact the exploit was added to the Metasploit framework
Impact:
- Remote code execution on vulnerable Citrix ADC and NetScaler Gateway instances.
- Unauthorized access to sensitive data and systems.
- Potential for lateral movement within networks.
Recommendations:
- Urgently patch affected systems by updating to the following versions: NetScaler ADC and NetScaler Gateway 13.1-49.13 and later releases, NetScaler ADC and NetScaler Gateway 13.0-91.13 and later releases of 13.0, NetScaler ADC 13.1-FIPS 13.1-37.159 and later releases of 13.1-FIPS, NetScaler ADC 12.1-FIPS 12.1-55.297 and later releases of 12.1-FIPS, NetScaler ADC 12.1-NDcPP 12.1-55.297 and later releases of 12.1-NDcPP.
- Monitor network traffic for any suspicious activities. Enterprise defenders are recommended to perform a check on all instances using the scripts released by Fox-IT and Mandiant.
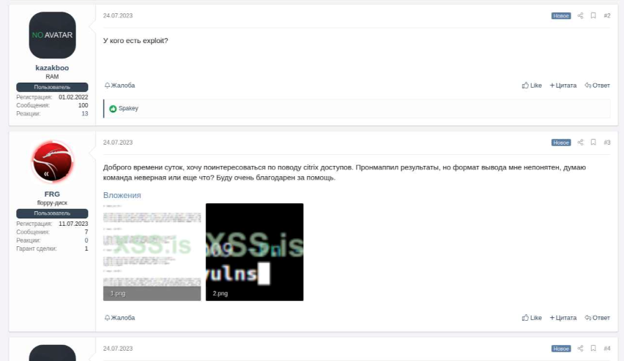
CVE-2023-27997 (XORtigate) affecting Fortigate
A critical pre-authentication remote code execution vulnerability in Fortigate, tracked as CVE-2023-27997 (also known as XORtigate), has attracted substantial interest among cybercriminals. This vulnerability was publicly disclosed in mid-June. Month after the disclosure and PoC publication, it was monetized by an actor named ‘FromHell’ who offered a custom exploit for sale at $5000 and sold it on the same day. The actor ‘FromHell’ was previously observed selling initial access to companies. Other actors have been noticed seeking custom exploits for this vulnerability.
Threat actor ‘FromHell’ advertises RCE vulnerability in Fortigate, based public exploits published on Github and Twitter
Impact:
- Remote code execution leading to unauthorized system control.
- Potential for data theft, lateral movement, and network compromise.
Recommendations:
- Immediately apply the provided patches to Fortigate devices by updating the following products: FortiOS-6K7K/FortiOS version 7.0.12 or above, FortiOS-6K7K/FortiOS version 6.4.13 or above, FortiOS-6K7K version 6.2.15 or above, FortiOS-6K7K/FortiOS version 6.0.17 or above, FortiProxy version 7.2.4 or above, FortiProxy version 7.0.10 or above, FortiProxy version 2.0.13 or above, FortiOS version 7.4.0 or above, FortiOS version 7.2.5 or above, FortiOS version 6.2.14 or above.
- Follow hardening recommendations, for example, FortiOS 7.2.0 Hardening Guide.
- Keep monitoring for any unusual network activities.
CVE-2023-34124 affecting SonicWall devices
In July 2023, SonicWall released patches addressing 15 security flaws in its GMS and Analytics software suites, including CVE-2023-34124, a web service authentication bypass, which is potentially leading to unauthorized access and exposure of sensitive information. Recent discussions within a cybercrime forum have highlighted threat actors’ keen interest in exploiting CVE-2023-34124, with them engaging in conversations about potential tools, techniques, and challenges. For example, threat actors are interested in finding scanners for the vulnerability, sharing possible vulnerable IPs, as well as attempting to overcome issues related to the exploit featured in Metasploit.
Chatter discussing SonicWall CVE-2023-34124
Impact:
- Unauthorized access to critical systems.
- Exposure of sensitive data to unauthorized parties.
- Compromise of infrastructure security.
Recommendation:
- Upgrade to the patched versions provided by SonicWall: GMS – Virtual Appliance 9.3.9330 and higher versions, GMS – Windows 9.3.9330 and higher versions, Analytics- Analytics 2.5.2-R9 and higher versions.
- Monitor systems for any signs of unauthorized access or compromise.
CVE-2022-24834 affecting Redis
Redis versions with Lua scripting support have been discovered to be susceptible to a heap overflow vulnerability (CVE-2022-24834). This vulnerability could potentially lead to remote code execution. PoC for the vulnerability was published nine days after its disclosure. While the vulnerability was patched and seemed to affect only authenticated and authorized users, it raised interest to similar Redis vulnerabilities. KELA observed a threat actor “dannon” is seeking to buy two adaptations of a publicly available PoC on the Exploit forum; the actor specified they need to work on different Redis’ versions, than the ones affected by the exploit. The specific versions of Redis for which “dannon” requires the exploit are 6.2.4 and 6.2.6. The initial offer was $500, but it has been raised to $1,000, probably for raising interest among other forum participants.
Impact:
- Remote code execution on affected Redis instances.
- Unauthorized access to data and potential network compromise.
- Successful exploitation of this vulnerability could lead to Denial of Service (DoS).
- Prompt upgrade affected Redis versions to those with fixed patches, as of now, the problem is fixed in versions 7.0.12, 6.2.13, 6.0.20.
- Strengthen access controls and consider IP whitelisting for accessing Redis.
- Monitor Redis instances for signs of exploitation.
Threat actor ‘dannon’ seeking a publicly available POC for different versions of Redis
Potential zero-days
In an evolving cyber threat landscape, threat actors are continually exploring new avenues to exploit vulnerabilities and gain unauthorized access. This month’s most interesting discussions were related to potential zero-days in Windows and TP-Link routers.
Threat actor Vinki claimed to discover a zero-day Local Privilege Escalation (LPE) vulnerability affecting Windows 7 to Windows 11 and Windows Server 2008 to Windows Server 2022. The actor said the vulnerability allows attackers to escalate their privileges from domain user to system, and that the exploit has been tested and confirmed to work on both 32-bit and 64-bit versions of Windows. The exploit is being offered for sale at a high price of $200,000, with negotiations possible. The threat actor Vinki has been active since the beginning of 2023 on the XSS forum and usually participates in different vulnerability-related activities, also seen giving advice to other threat actors. So far, the actor made two guarant-deals via XSS, which adds to the credibility of the offer.
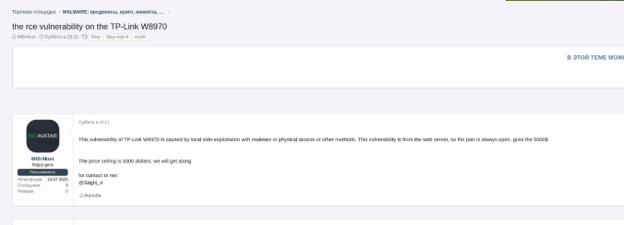
Another potential zero-day remote code execution (RCE) vulnerability was offered for sale by the threat actor ‘Mi0r4kun’ and allegedly affects TP-Link W8970 routers. According to the actor, the vulnerability, originating from the router’s web server, requires local side-exploitation with malware, physical access, or other methods, and then allows remotely control of the devices. The price set for this vulnerability is $5000. TP-Link routers have frequently become targets of attacks, recently being abused by the Chinese APT Camaro Dragon with the use of a malicious firmware implant tailored for TP-Link routers.
Threat actor ‘Mi0r4kun’ offering RCE vulnerability affecting TP-Link W8970 routers for USD5000
Cybercrime chatter adds context to information about disclosed vulnerabilities and provides valuable insights into emerging threats, helping companies take proactive measures to defend against attacks, and contributing to overall cybersecurity awareness and preparedness. KELA recommends using this information for:
- Prioritization of patching and mitigation efforts. Tracking discussions on cybercrime forums allows a company to stay informed about the latest vulnerabilities being targeted by attackers and apply patches in a timely manner.
- Risk assessment. Understanding which vulnerabilities are actively being discussed on cybercrime forums enables a company to assess its risk exposure and make informed decisions about allocating resources to address the most critical vulnerabilities.
- Proactive defense against real attack techniques. Monitoring these forums provides insights into the methods and tools that cybercriminals are using to exploit vulnerabilities. This information can be used to fine-tune defensive strategies and train security personnel.
Incident response planning. If a company knows about vulnerabilities that are actively being exploited or discussed, it can develop targeted incident response plans. This ensures that they’re prepared to react swiftly and effectively if an attack occurs.
Get notified about threats targeting your organization in real-time. Try KELA’s Cyber Threat Intelligence Platform for Free.