The Vacation Trap: Inside the Booking.com & VECT-TeamPCP Collaboration
In April 2026, Booking.com - a $137 billion titan of the travel industry - confirmed a major security breach that exposed sensitive users' data. Intruders compromised internal systems and lurked undetected for weeks, representing a potential critical risk in the reservation architecture that facilitates millions of global journeys. Here is KELA's breakdown of the compromise, the threat actors involved, and the potential vectors that made it possible.
Updated April 15, 2026

The Playbook: Weaponizing Trust
The attackers abandoned standard, easily detectable phishing in favor of high-fidelity social engineering. By infiltrating the native platforms guests already trust, they effectively bypassed user skepticism using three main vectors:
- Spoofed Email Communications: Sophisticated, branded emails claiming "suspected activity" to harvest credentials and hijack sessions and awareness regarding an incident .
- WhatsApp Exploitation: Highly targeted phishing messages containing real-time, accurate booking details to quickly build victim confidence.
- In-App Chat Injection: The most alarming tactic. Attackers hijacked compromised property management portals to insert fraudulent, high-pressure messages directly into legitimate guest-host chats. These messages demanded immediate, off-platform payments under the threat of canceling the reservation “within 10 days”.
The Fallout: Exposed PII
While Booking.com maintains that no direct financial data was stolen, the strategic risk of the exposed data is immense. This information is premium fuel for secondary identity theft and targeted fraud. Exposed data includes:
- Full Names, Emails, and Phone Numbers
- Detailed Reservation Records (dates, locations, property specifics)
- Direct Communication Histories between guests and accommodations
The Threat Actors: A Dangerous New Alliance
Current intelligence observed by KELA strongly attributes this breach to a newly formed "Crime-as-a-Service" alliance between VECT (a ransomware group with robust extortion infrastructure) and TeamPCP (cyber criminal operation also known to be collaborating with additional ransomware operations and being behind sophisticated supply chain attacks).
Strategic markers tracking this alliance include:
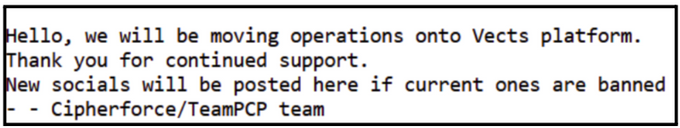
- March 2026: VECT formally announced their collaboration with TeamPCP on BreachForums to leverage supply chain attack vectors. Additionally KELA observed a note on the CipherForce ransomware blog indicating a wider collaboration between operations.
A note on CipherForce ransomware blog, March 2026
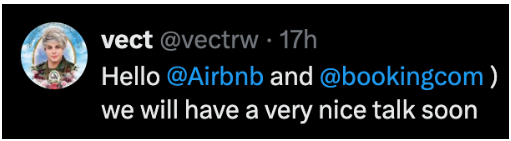
- April 13, 2026: User named VECT posted a precursor threat on X targeting Booking.com and Airbnb, stating: "we will have a very nice talk soon."
VECT’s post on X, April 13, 2026
Potential Initial Access Vectors
While the investigation is ongoing, potential initial access vectors include:
- Compromised Partner Accounts: Threat actors possibly utilized credential stuffing, phishing, or purchased logs to hijack the accounts of individual hotel partners and property managers.
- Third-Party Supply Chain Attacks: Exploitation of vulnerabilities within the external Property Management Systems (PMS) or channel managers that interface directly with Booking.com's API.
- Infostealer Malware: Harvesting session tokens and login credentials from employees or affiliated hosts to quietly bypass multi-factor authentication.
The ransomware landscape is wide and fiercely dynamic, but our collection engines never sleep. KELA is constantly gathering intelligence and monitoring the latest shifts in ransomware operations to keep you one step ahead of the threat.