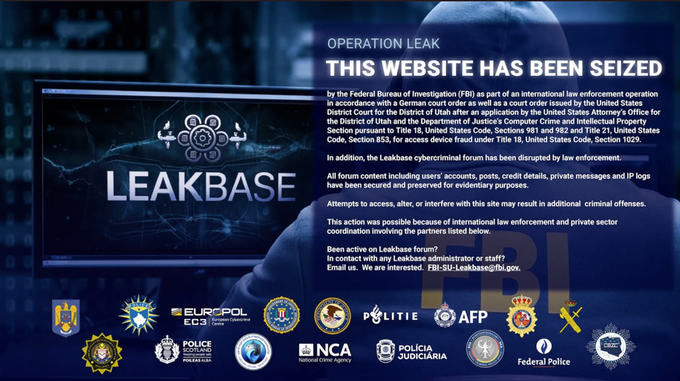
Law enforcement seizes Leakbase
The Event: Operation Leak dismantling a major hub
Updated March 5, 2026
In a massive coordinated effort dubbed Operation Leak, international law enforcement agencies led by the FBI and Europol have officially dismantled LeakBase (leakbase[.]la).
On March 4, 2026, the site's domain was seized and replaced with an official law enforcement notice.
The takedown was executed in two phases. March 3 saw rapid, coordinated physical interventions, including arrests and house searches, targeting the forum’s 37 most active users across 14 countries. The following day, authorities seized the platform’s infrastructure, domain, and its entire database, moving the operation into an active prevention and prosecution phase.
What Was LeakBase?
Leakbase is/was a cybercrime forum launched around 2021 that operated on the open web (not only on the dark web) through multiple domains. It served as a marketplace and community where cybercriminals could share, sell, and access stolen data obtained from past breaches or malware infections.
The platform hosted large databases containing hundreds of millions of compromised credentials, including usernames, passwords, credit and debit card numbers, banking information, and other personally identifiable or corporate data. These datasets were often used to support activities such as account takeovers, fraud, and further cyber intrusions.
Before its demise in early March 2026, the forum boasted:
- 142,000 registered users
- 32,000 public posts
- Over 215,000 private messages
Interestingly, despite its global English-speaking user base, LeakBase strictly prohibited the sale or publication of data related to Russian entities, a strong indicator that the forum's administrators were either based in Russia or sought to avoid the crosshairs of local authorities.
Actor Reactions
Chatter in the Underground KELA observed an ongoing active chatter discussing the shutdown across multiple underground platforms, including XSS, Exploit, BreachForums, and Telegram channels. While law enforcement's seizure of private communications and IP logs often triggers sheer panic, the actual sentiment across the ecosystem right now is a mix of paranoia, mockery, and opportunism:
- Skepticism and Mockery: Many cybercriminals scoffed at law enforcement's official characterization of LeakBase. Users on BreachForumsReborn actively mocked the FBI’s press release, calling the claim that it was 'one of the world’s largest hacker forums' a 'joke.' Several actors dismissed LeakBase as a 'dead forum' or a 'skid forum,' joking about the administrators' poor operational security and speculating they 'prob left their kali boxes exposed on their home ips.'
- Paranoia and Self-Preservation: Despite the outward bravado, the arrests and data seizures hit a nerve. Actors expressed concern for their own safety, wondering aloud who the '37 most active users' arrested actually were. Others openly worried about the resilience of top-tier forums, hoping platforms like Exploit are 'strong enough to handle the attacks of the FBI.' Users were quick to warn each other about the dangers of having registered accounts on targeted platforms.
- Sympathy and Opportunism: While some users expressed well wishes for the captured leadership ('RIP. hope chucky is aight' and 'hope admin safe'), others immediately looked for ways to capitalize on the takedown, such as posting requests to acquire the leaked LeakBase forum source code
What Happens Now & Where Will Users Go?
With LeakBase gone, a vacuum has opened in the mid-tier data brokering market. Based on historical trends from similar takedowns (like RaidForums or BreachForums), we assess that displaced users will likely migrate to:
- Telegram Channels: A significant portion of the stealer-log trade will move to decentralized, invite-only Telegram groups to avoid domain seizures.
- Established Russian-speaking Forums: Top-tier actors looking for stability may attempt to migrate to established strongholds like XSS or Exploit, new versions of BreachForums, and DarkForum, though the barrier to entry there is much higher.
- New Spinoff Forums: We anticipate the launch of new English-speaking forums attempting to claim the 'LeakBase' mantle within the next few weeks, though many users will initially view them with extreme suspicion, fearing they are law enforcement honeypots.
Identifying Leakbase's Owner: Chucky
KELA’s CIC investigated the cybercriminal known as 'Chucky', beginning with WebMoney IDs he shared early in his activity, which indicated that the account was registered in Taganrog, Russia, supported by official documents submitted to the platform. Further research on a forum where Chucky was active in 2013 uncovered threads related to gifting items to VK profiles. Although most of his posts were deleted, likely for OPSEC reasons, one remaining comment referenced sending a gift to a girl from Taganrog. By cross referencing quoted messages in the same threads, KELA identified that he previously used the moniker 'beakdaz'.
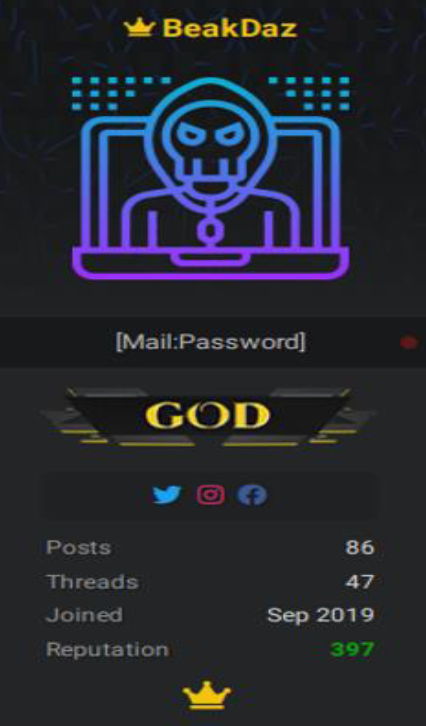
Investigation of the username 'beakdaz' across multiple platforms revealed accounts on services such as GitLab, Gravatar, ImageShack, and Keybase, some featuring a profile picture of the character Chucky, as well as appearances in leaked data from cybercrime forums including Lolzteam and RaidForums. The username was linked to a Rambler email address that appeared in multiple breaches. Activity under the 'beakdaz' alias on RaidForums between 2019 and 2022 included sharing databases later posted by 'Chucky' on LeakBase. The Telegram account @beakdaz was also tied to the same Telegram ID used by the LeakBase administrator, further linking the aliases.
Posts by Chucky that has been deleted, in his activity dating back to 2013
Further OSINT and data leaks analysis of the email address and the 'beakdaz' profiles identified several social media accounts and a VK profile linked to an individual from Taganrog. Additional evidence from leaked Russian databases connected the same email address, multiple phone numbers, and other online accounts to this individual. The phone numbers were also linked to the Skype account used by 'Chucky', @shum_dozhdya. These identifiers further led to additional emails, usernames, and online accounts associated with the same individual, tying his activity to earlier cybercrime personas dating back to 2009.
The full set of associated identifiers and historical activity is available to KELA customers through the platform.
Based on the combined evidence, KELA assessed with high confidence that the aliases 'Chucky', 'beakdaz', and the LeakBase administrator are operated by the same individual.
Chucky previously used moniker on RaidForums, BeakDaz
Defender Recommendations
Key Actions:
- Prioritize Credential Mitigation: LeakBase specialized in hosting and selling large databases of compromised credentials, including usernames, passwords, and banking information, often used for account takeovers.
- Zero Trust & Identity Controls: Apply Zero Trust principles across cloud, developer, and SaaS environments. Enforce phishing-resistant MFA (FIDO2/WebAuthn) for privileged accounts, and implement strict session/token lifecycle management with automated revocation for suspicious activity.
- Ensure Enforcement of MFA for Mission Critical Services: Implement and enforce strong Multi-Factor Authentication (MFA) across business or mission-critical services to render any stolen static credentials ineffective.
- Monitor for Exposure: Use threat intelligence platforms like KELA to actively check for your organization’s credentials, PII, and corporate data within breached datasets or stealer-log offerings.
- Adjust Threat Monitoring Coverage: The dismantling of LeakBase will create a temporary vacuum and displace users, requiring defenders to shift their focus.
- Monitor Telegram: Dedicate increased resources to monitoring decentralized, invite-only Telegram channels, as a significant portion of the stealer-log trade is expected to move there to avoid domain seizures.
- Monitor New Spinoffs with Caution: Closely monitor the expected launch of new English-speaking forums, but approach them with extreme suspicion as actors fear they might be law enforcement honeypots.
- Track High-Tier Forums: Be prepared for an influx of new, established actors attempting to join top-tier forums like XSS and Exploit for stability. Ensure adequate monitoring of these high-barrier-to-entry strongholds.
- Leverage Attribution Intelligence: The detailed identification of the administrator 'Chucky' highlights the importance of attribution. Utilize platforms like KELA that provide associated identifiers and historical activity for key cybercriminals to enhance your own internal threat modeling and attribution efforts.