Inside The Gentlemen Leak: How a New RaaS Captured 10% of 2026’s Global Ransomware Victims
KELA’s deep dive into the 2026 Gentlemen Ransomware leak. See how they used Black Basta’s playbook and AI vibe-coding to become the world's #2 RaaS operation.
Updated May 14, 2026
TL;DR
On May 4, 2026, KELA observed that partial internal chats and alleged backend data tied to The Gentlemen RaaS operation were advertised across several underground forums. Analyzing the so far leaked materials, containing both text-based chats and images, spanning a nearly six-month timeframe, beginning on November 7, 2025 and ending on April 30, 2026, has provided a rare visibility into the group’s internal structure, affiliate model, infrastructure, tooling, targeting logic, use of AI, and relationships with collaborators and other ransomware ecosystems. The leak offers an inside look at how a relatively new but highly active ransomware program coordinates intrusions, evaluates victims, supports affiliates, and professionalizes its operations.
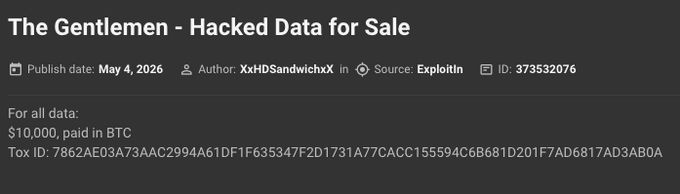
The leak, which is similar to the major Black Basta internal chat leak from February 2025, initially surfaced as a listing post on Exploit.in by XxHDSandwichxX on May 4, 2026. It was later shared by two other users, suspected to be the same actor: user n7778 on Cracked forum on May 5, 2026, and by n789 on Nulled the same day.
The seller framed the material as internal Gentlemen communications and priced the full dataset at $10,000 in BTC and listed a Tox contact for samples. Samples reportedly began leaking on May 6, and the Exploit.in account was later banned.
The Gentlemen leak by XxHDSandwichxX on Exploit.in | KELA Platform
The Gentlemen - a RaaS Rising
From January 1, 2026 to May 13, 2026, KELA has tracked a total of 3,349 publicly claimed ransomware victims - approximately a 14.50% increase compared to the number of total claimed attacks in the same time period of 2025.
According to KELA’s data lake, as for January to May 2026, the top active ransomware group was the Qilin RaaS operation, who claimed 17% of the total publicly claimed ransomware attacks, with the second place going to a new rising competitor - The Gentlemen.
The Gentlemen operation, which has been active since around September 2025, has been progressing quickly with 328 publicly claimed victims during the first five months of 2026 alone, meaning their claims account for 10% of the total global ransomware claims so far in 2026.
The Distinguished Gentlemen
Right off the bat the chats reveal the visible inner working circle of gentlemen members - zeta88, Wick, mAst3r, Kunder, qbit, quant, Protagor, and JeLLy. The chats do not show a rigid hierarchy, but rather a RaaS-like ecosystem around The Gentlemen: a core administrator/operator layer, hands-on intrusion actors, access-focused collaborators, tooling contributors, and external partners or affiliates. Based on the observed chats, the roles appear as follows:
- zeta88 - apparent core administrator/operator; manages the panel, locker/encrypter, infrastructure, affiliates, negotiations, and gets 10% cut of the ransom payment.
- Wick - hands-on intrusion/encryption actor; involved in target work, access, reconnaissance, data theft, and encryption, often collaborating with mAst3r.
- mAst3r - hands-on collaborator focused on target selection, recon, and support during intrusion/encryption activity.
- Kunder - suspected as the access-focused collaborator and victim-environment validator. Kunder’s role looks more than passive access resale, but less administrative than zeta88.
- qbit - possibly working on tooling and vulnerability research.
- quant - appears to contribute with accesses from logs, brute-force capacity, phishing ideas, and collection tools.
- Protagor and JeLLy - supporting actors in tooling, access, or operational discussions.
- Hastala/hastalamuerte - seems to be an initial access broker (IAB) working with the group. The chats show other actors waiting for Hastala to provide or select targets/networks, suggesting an IAB-like role, though the exact commercial arrangement is not fully visible in the sampled chats.
- Dragon Force (DragonForce), Devman, LockBit, Qilin, and the already inoperative Black Basta are among those referenced as adjacent groups, competitors, partners, or ecosystem touchpoints.
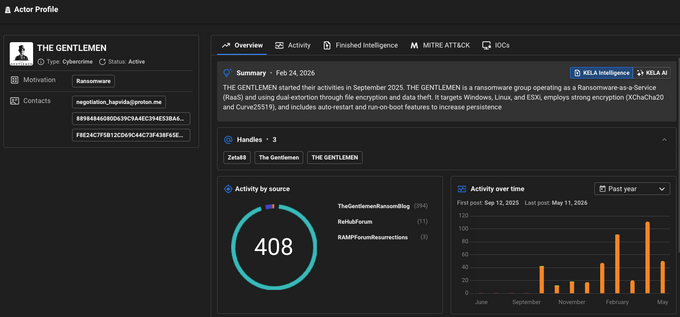
The Actor Profile of The Gentlemen and Zeta88 - one of the group’s active and public representatives | KELA’s Actor Hub
The Gentlemen’s Infrastructure and Arsenal
Following a migration away from a platform they deemed “awful” (Mattermost), the core team set up shop on what they thought was a fortified self-hosted Rocket.Chat .onion instance. However, the irony of underground infrastructure wasn't lost on them. zeta88 was actually plotting a move to a faster, Rust-based chat alternative to Rocket, but not before the internals were leaked.
According to the chats, for external communications and victim negotiations, the group relies on a Tor Data Leak Site (DLS), Tox, Session, and Element. Their attack traffic is routed through a web of bulletproof VPS providers (such as 4vps.su and JustHost.asia) utilizing Amnezia VPN, WireGuard, and Cloudflare ZeroTrust tunnels orchestrated by custom tools like ZeroPulse.
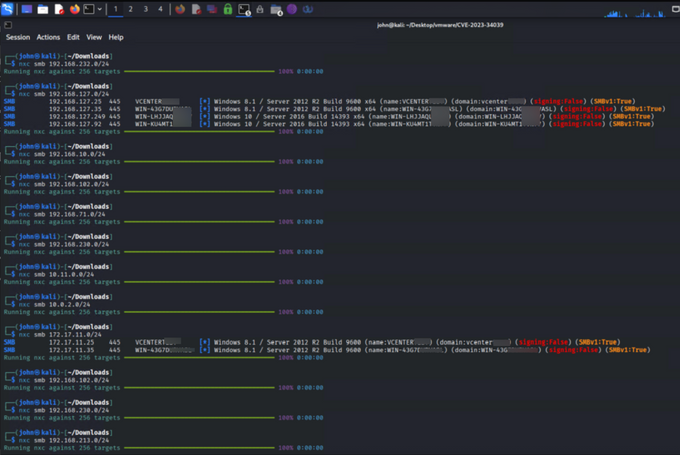
According to the leak, the group actively scans for vulnerabilities such as CVE-2023-34039 (as can be seen in the screenshot below), CVE-2025-33073, CVE-2024-55591 for FortiOS management access, and the Erlang SSH vulnerability CVE-2025-32433 targeting Cisco devices. Still, they are just as happy to rely on classic misconfigurations, chaining together PetitPotam, PrinterBug, WebDAV WebClient exposures, ZeroLogon, and even exploiting iDRAC or Veeam backup servers to achieve Domain Admin. When all else fails, they abuse the Windows MSI service via RegPwn to quietly elevate privileges right under the victim's nose.
A screenshot of scanning CVE-2023-34039 on a target's environment | The Gentlemen Leak
AI in Ransomware: How The Gentlemen Use 'Abliterated' LLMs
One of the most interesting findings is the group’s practical and selective use of AI. zeta88 says he “vibe-coded” a panel in three days, but stresses that AI output still requires understanding and manual correction. He and others distinguish between models for different purposes: Chinese or uncensored models such as Qwen, DeepSeek, Kimi, Ernie/Baidu, and chat.z.ai are discussed for coding and technical tasks. The chats also show LLMs being used for technical lookup, such as Jira mass-mailing and FortiGate internals.
The chats also show interest in malicious LLM variants, rather than only mainstream AI assistants. qbit shared a model called Huihui-Qwen3.5-35B-A3B-abliterated, describing it as a “radical neural network” that can create any content “without censorship,” with “all barriers removed,” “complete absence of refusals,” and “absolutely no restrictions.” Separately, Protagor suggested renting GPU capacity on Vast.ai and using Qwen 3.5 to process hundreds of gigabytes of stolen victim data, identify panels, and reason over access paths.
Reusing Leaked Ransomware Playbooks: Learning from Black Basta
KELA observed that the leak is reminiscent of the major Black Basta internal chat leak from February 2025. Notably, the leaked communications show that The Gentlemen members actively studied Black Basta’s leaked materials and operational workflows.
The discussions focused heavily on Black Basta’s phishing and initial access methodologies. Members analyzed screenshots from the leaked chats to understand whether Black Basta distributed phishing emails broadly through Microsoft infrastructure or first compromised corporate mailboxes and then abused trusted internal email accounts to deliver more convincing, whitelisted messages. The shared screenshots outlined an OWA-driven workflow in which actors leveraged valid mailbox access, reviewed the victim organization’s revenue and profile, identified exposed infrastructure through reconnaissance platforms such as Censys, and tested stolen credentials against VPN, Citrix, Cisco, Fortinet, RDP, and other remote-access services.
The leaked Black Basta chats also highlighted the group’s focus on high-quality social engineering. In one exchange, an actor rejected generic phishing templates in favor of short, natural colleague-to-colleague messages such as “Hi, look at the document.” Additional screenshots referenced impersonating internal employees, reviewing email threads to craft believable replies, and selecting targets based on financial value. The discussions suggest that The Gentlemen viewed the Black Basta leak as a practical playbook for improving phishing, credential reuse, and internal reconnaissance techniques.
Overall, the leak provides insight into an increasingly competitive ransomware ecosystem in which threat actors continuously analyze each other’s tradecraft, operational mistakes, and successful intrusion methods in order to refine their own operations.
Initial Access Tactics: OWA Abuse and Email-Based Extortion
As for the initial access vector, The Gentlemen experimented with compromised Outlook Web Access (OWA) as both an initial-access source and a delivery channel for phishing, payload staging, and extortion pressure.
While analyzing the leaked materials, which include both text-based chats and images, KELA observed a leaked screenshot from the chats of The Gentlemen that suggests a method of blackmailing victims using sensitive medical content, and possibly doing so using the personal mailbox of the victim.
The screenshot showed an extortion-style email message that threatens escalation by notifying affected individuals related to the victim. The message includes sensitive medical/patient-style data, and its operational significance is clear: The Gentlemen were not only discussing OWA accounts as a way to find VPN credentials or for phishing attempts; they were also testing or using compromised mailboxes as a trusted delivery and pressure channel in extortion workflows. This blurs the line between access validation, phishing, and ransomware negotiation support.
The RaaS Model and Target Preference
The target-selection logic is pragmatic. The chats show how Wick tells mAst3r to prioritize Tier 1–3 countries or Latin America and avoid India/Africa-style targets, but also explains that raw revenue is not enough: a $20M utility can be better than a $200M manufacturer if operational disruption creates more pressure. Other than geography, revenue and sector, they evaluate LDAP presence, panel availability, domain-admin likelihood, data value, file shares, cloud posture, and how much a complete “lock” would really hurt the business.
The internal chats also largely confirm The Gentlemen’s public RaaS pitch, but provide some operational details. In public, the group advertised a 90/10 split, affiliate-controlled negotiations, and builds issued under the affiliate’s Tox. Internally, zeta88 described the same model more concretely: custom ransomware executable builds are generated through the panel which is a part of the RaaS package, ransom notes include the affiliate’s Tox and Session, victims who contact the administrator are redirected to the affiliate, wallets belong to the affiliate, and zeta88 receives 10%.