Beyond the Regime: How Iran Weaponizes Cybercrime and Ransomware Tactics
When U.S. organizations think of ransomware, the immediate image is often a financially motivated, Eastern European cybercriminal cartel operating a massive Ransomware-as-a-Service (RaaS) empire. However, a different, hybrid threat has emerged from the Middle East. While Iran may not operate traditional, large-scale ransomware cartels like LockBit or ALPHV, Iranian state-sponsored threat actors have increasingly blurred the lines between Advanced Persistent Threat (APT) operations and everyday e-crime. They aren't just adapting to the cybercrime ecosystem; they are weaponizing it. From acting as Initial Access Brokers (IABs) to deploying pseudo-ransomware for destructive attacks, Iranian groups leverage cybercrime tactics to support state objectives (while some examples discussed below involve incidents outside the U.S., they serve as critical analog cases illustrating the methods relevant to U.S. critical infrastructure defenders). Here is what defenders need to know about the evolving Iranian playbook.
Published March 28, 2026

Ransomware Enablement and Direct Collaboration
One of the most concerning developments is the direct collaboration between Iranian state-linked actors and the traditional ransomware ecosystem.
A joint advisory from the FBI, CISA, and DC3 in August 2024 highlighted groups like Pioneer Kitten (also known as UNC757 or Fox Kitten). Instead of deploying their own bespoke ransomware across the board, these actors specialize in exploiting vulnerabilities in internet-facing edge devices (such as VPNs and firewalls). Once they establish a foothold in a network, Iran-based actors have collaborated directly with affiliates from NoEscape, RansomHouse, and ALPHV/BlackCat, sharing access in exchange for a percentage of the ransom proceeds.
This provides Iranian actors with an additional revenue stream through financially motivated cyber activity, while traditional ransomware groups gain facilitated access to US schools, healthcare facilities, and financial institutions.
State-Aligned RaaS and the Current War: The Pay2Key Escalation
Perhaps the clearest example of Iran weaponizing the cybercriminal ecosystem for geopolitical retribution is the evolution and recent resurgence of the Pay2Key ransomware.
Originally emerging in late 2020, Pay2Key - attributed to the Iranian state-aligned group Fox Kitten - was initially used in highly targeted campaigns against Israeli organizations. These early attacks blended extortion with state-sponsored information warfare, as operators publicly taunted victims and leaked data to incite panic and punish adversaries.
However, catalyzed by the ongoing regional war and heightened geopolitical tensions, Pay2Key has aggressively "woken up" and expanded its operations to act as a punitive arm of the Iranian state. Recent campaigns have demonstrated a clear shift toward high-impact US targets. Notably, reporting indicates that this Iran-linked ransomware gang has specifically targeted US healthcare organizations, a move designed to cripple vital life-safety services and exert maximum pressure during a geopolitical crisis.
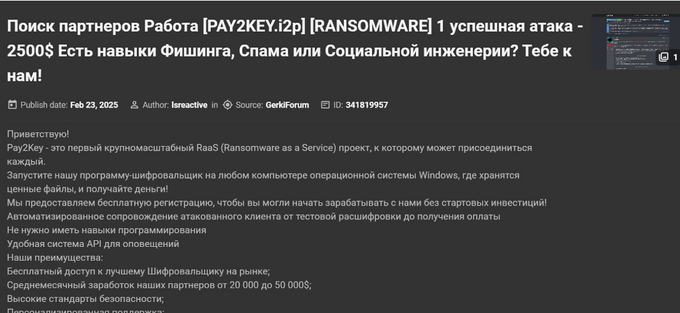
Threat intelligence reports highlight a significant and dangerous operational evolution. In 2025, the group resurfaced as Pay2Key.I2P, operating a highly professionalized Ransomware-as-a-Service (RaaS) platform heavily reliant on the anonymous I2P network. Utilizing a variant of the potent Mimic ransomware, the group actively recruits skilled affiliates, particularly aiming to tap into the Russian cybercrime underworld, to conduct attacks on their behalf.
The threat actor "lsreactive" advertising the Pay2Key Ransomware-as-a-Service (RaaS) program on a Russian underground forum | KELA Platform
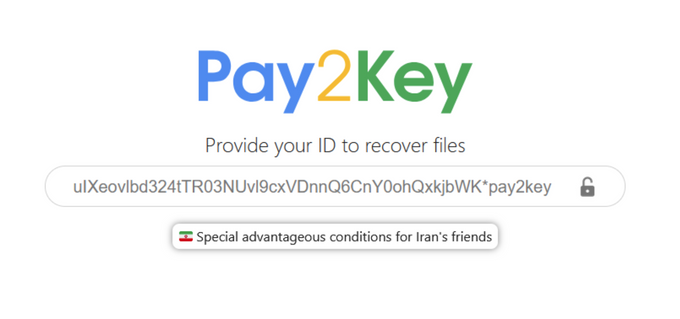
Pay2Key.I2P’s platform offering “Special advantageous conditions for Iran’s friends”
What sets Pay2Key apart from traditional financial cybercriminal cartels is its explicit state-aligned agenda. To incentivize the targeting of Iran's geopolitical adversaries involved in the current conflict, the RaaS operators offer an enhanced profit share - increasing the affiliate's cut from 70% to 80% - if they successfully execute attacks against designated "enemies" of Iran, primarily the United States and Israel. This bounty system perfectly illustrates the hybrid threat: Iran is effectively outsourcing geopolitical retribution to the global cybercrime talent pool, creating a powerful, scalable force multiplier for its state operations.
Pseudo-Ransomware and Destructive Smokescreens
In standard e-crime, the encryption of files is the primary mechanism for financial gain. For Iranian actors, ransomware-style encryption is frequently used as a disguise for data destruction, sabotage, or political retribution.
Public reporting suggests multiple instances where Iranian-linked groups deployed what appears to be ransomware, but the operation's nature indicated distraction or disruptive goals rather than financial gain:
- The Agrius APT and Apostle: A prime example is the Agrius group and their use of the Apostle malware. Originally analyzed as a data wiper, it was later retrofitted to function as a ransomware variant. Wrapping destructive wipers in the guise of financial extortion allows actors to obscure their geopolitical motives and complicate incident response.
- Operation "Homeland Justice" (Albania): In July 2022, an Iranian state-sponsored actor launched a coordinated cyberattack against Albanian government networks. The attackers deployed a bespoke ransomware called ROADSWEEP alongside a possible destructive wiper malware (ZeroCleare). The operation used ransomware-style encryption in a politically motivated disruptive campaign, heavily indicating that chaos, rather than ransom collection, was the primary goal.
Front Companies and the "Moonlighting" Phenomenon
Complicating attribution further is the trend of "moonlighting" among Iranian cyber operators, where state-sponsored capabilities are used for independent financial gain.
A clear example emerged in April 2024, when the US DOJ and Treasury Department took action against individuals working for Mahak Rayan Afraz, an Iran-based technology company functioning as a front for the IRGC Cyber-Electronic Command (IRGC-CEC). While officially conducting state-sponsored operations, these individuals frequently use their state-provided access and expertise to moonlight. They execute ransomware-style extortion against opportunistic targets purely for personal financial enrichment.
Geopolitical Escalation and the OFAC Attribution Nightmare
The ongoing geopolitical conflict involving Iran has fundamentally shifted the threat landscape, turning US organizations into what Iranian actors perceive as legitimate targets. Within this unstable environment, the lines between state-sponsored cyber warfare and opportunistic cybercrime have completely dissolved. The same state apparatus that sponsors purely destructive or hacktivist campaigns is deeply intertwined with the cybercriminal underground.
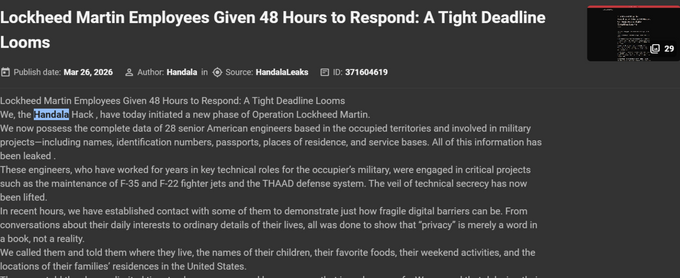
A recent publication by Handala claiming an alleged breach of Lockheed Martin, featuring leaked personal details of American engineers and a threatening 48-hour deadline | KELA Platform ; Handala operates as an Iranian state-sponsored proxy, conducting cyberattacks and psychological warfare against Israeli and Western targets under the guise of a pro-Palestinian hacktivist group
For US organizations, this blending of state and criminal activity creates a massive legal and operational risk: the attribution nightmare. If a company falls victim to a successful ransomware or extortion event, identifying the true threat actor is no longer just an IT problem - it is a critical compliance issue. Because Iranian state actors and their proxies are heavily sanctioned by the US Department of the Treasury’s Office of Foreign Assets Control (OFAC), paying a ransom to a seemingly independent group that is secretly an Iranian front (or an IAB sharing profits with Iran) could result in severe legal and financial penalties.
This complexity underscores why traditional security alerts are insufficient and why continuous monitoring of actor relationships is essential.
Defending Against the Hybrid Threat
Understanding that an attack might present as standard ransomware but actually be a state-linked operation is crucial. To defend against these tactics, organizations must implement foundational resilience measures alongside proactive controls:
- Prioritize Edge Device Patching and Validation: Iranian actors heavily target unpatched, internet-facing appliances. Prioritize patching these devices, but crucially, validate the systems for signs of prior compromise and persistence, as patching alone does not evict an attacker who is already inside.
- Upgrade to Phishing-Resistant MFA: Prioritize phishing-resistant MFA (for example, FIDO2, security keys, or passkeys), especially for external access and privileged accounts. This mitigates the risk of AiTM attacks and MFA fatigue tactics often utilized by these groups.
- Strict IT/OT Segmentation and Hardening: Segment IT and OT networks entirely to prevent initial access footholds from pivoting into critical operational environments. Organizations must remove PLCs from direct internet exposure, change all default credentials, and require MFA for remote OT access.
- Establish Foundational Resilience: Ensure you have offline, regularly tested backups, centralized logging, and updated incident response playbooks. Participate in information-sharing organizations (like ISACs).
- Leverage Proactive Threat Intelligence: Threat-intelligence monitoring can significantly improve visibility into adversary infrastructure and compromised credential markets. Partnering with a dedicated CTI vendor like KELA enhances your core controls, providing the necessary context and early warnings to respond effectively before data is encrypted or destroyed.
Need to Create Your Own Iranian Defense Playbook?
Contact our team of experts here