Revealing Corporate Vulnerabilities: Understanding How Threat Actors Breach and Exploit Your Data
Updated December 12, 2023

Threat actors engage in active infiltration of corporate assets, extracting valuable information and distributing it on cybercrime forums for trade. Records like contact details, social security numbers, and credit card information are used for financial gain.
Initial access vectors of cybercriminals can take various forms, such as exploiting vulnerabilities, deploying malware, conducting phishing attacks, leveraging compromised credentials, or employing other tactics like stealing information through third parties. Attackers frequently disclose their entry points on cybercrime underground forums. KELA monitored BreachForums, an English-speaking forum, which is one of the most popular cybercrime communities for stolen databases sharing to understand threat actors’ tactics, revealing a range of risks such as injection, misconfigurations, API vulnerabilities, and supply chain attacks. This analysis focuses on threat actors specializing in database stealing and trading, excluding more complex attacks discussed elsewhere.
Injection Vulnerabilities
One of the main security risks associated with web applications is injection. According to OWASP’s top 10 risks for 2021, injection was ranked as the top third vulnerability category. One of the most common injection’ types is SQL injection, which is an attack vector that executes malicious SQL code for backend database manipulation to access information that was not intended to be displayed.
KELA’s analysis shows that SQL injection is the most common vector exploited by threat actors leaking/selling databases on BreachForums, based on details shared by threat actors themselves.
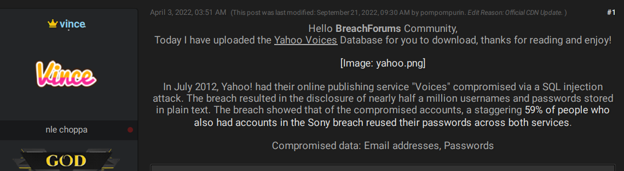
For instance, in January 2022, the threat actor ‘vince’ reposted a Yahoo database, stating that the company was compromised in 2012 through an SQL injection attack. The leak exposed approximately half a million email addresses and passwords associated with Yahoo! Voices. The passwords for the accounts were not encrypted, allowing any actor to reuse them for other malicious activities. While Yahoo confirmed that 400,000 accounts had been compromised, they claimed that less than 5% of them had valid passwords.
Actor reposting that Yahoo! Voices was breached in 2012 via SQL injection attack
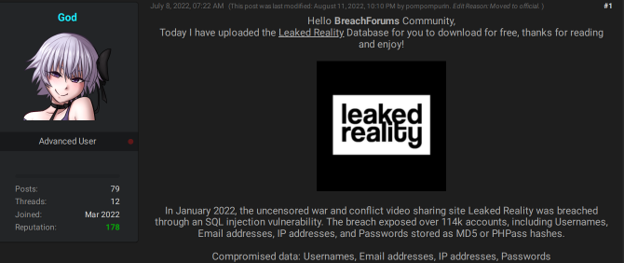
Actor sharing Leaked Reality database using SQL injection
How to Prevent?
- Secure coding practices: Use parameterized queries or prepared statements in database queries to prevent direct injection of user input.
- Input validation: Input validation and sanitization should be implemented to ensure that user inputs are properly formatted and do not contain malicious code.
- Security audits: Regular security audits can help identify and address potential SQL injection vulnerabilities.
- Monitoring: Monitor cybercrime sources to understand the interest of threat actors in SQL injection attacks and potential targets discussion.
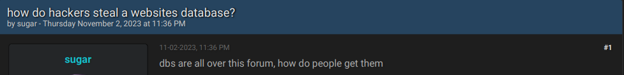
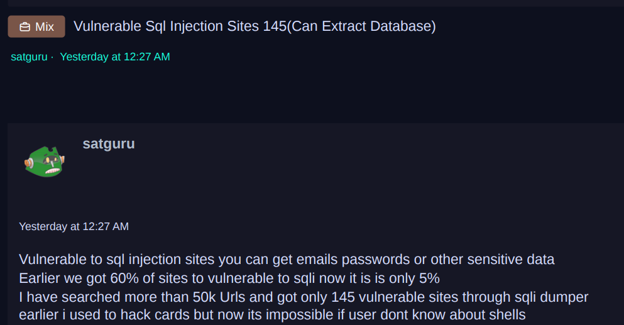
Actor asking how hackers obtain databases Another actor replies that SQL injection is the most common vector
Actor posting a list of vulnerable SQL injection sites
API Risks
API security risks can lead to data breaches and financial loss. According to OWASP’s top 10 API security vulnerabilities for 2023, the most common weaknesses stem from improper implementation of authentication mechanisms, exposing endpoints that handle object identifiers, unsafe consumption of third-party APIs, and more. According to OWASP rank, the most widespread API vulnerability is Broken Object Level Authorization, which can allow attackers to gain access to sensitive data. Object level authorization is an access control mechanism that is usually implemented at the code level to validate that a user can only access the objects that they should have permission to access. Failures in this mechanism typically lead to unauthorized information disclosure, modification, or destruction of all data.
Over the past years, some of the big data breaches occurred as a result of application programming interface (API) vulnerabilities. For example, in January 2023, threat actor ‘ThinkingOne’ shared a database of Twitter, which was allegedly scraped in the preceding two months. According to the actor, the leak exposed approximately 209 million records, and included users’ email addresses, full names, usernames, number of followers and account creation date. Twitter confirmed that a vulnerability was discovered in January 2022, allowing users to query any email/phone and retrieve a Twitter profile. The company later determined that threat actors exploited this flaw, offering the data for sale. The 2023 leak was exposed through the same vulnerability discovered in January 2022.
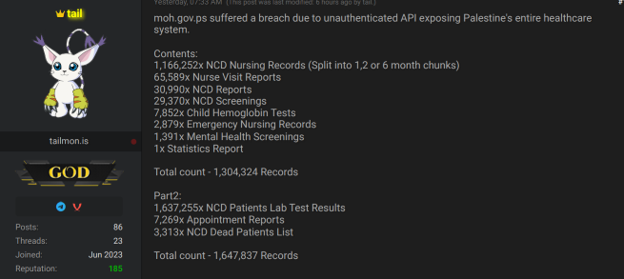
Additional examples of data breaches stemming from exposed APIs can be found on cybercrime forums. Recently, the actor ‘tail’ shared a database of Palestinian Authority’s healthcare system that exposed approximately a million records through unauthenticated API.
Actor sharing a database of records from Palestinian Authority’s healthcare system
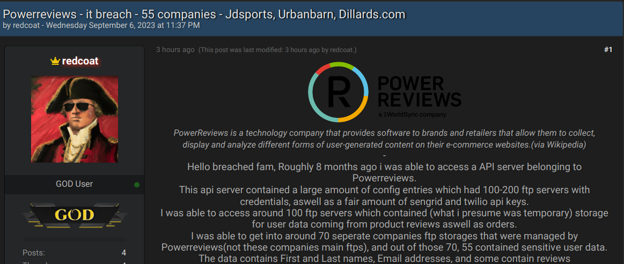
Another actor offered for sale a database of a technology company. The actor claimed that he had been able to attack the company through API server access. Allegedly, the API server contained a large amount of data, including FTP servers’ credentials, which allowed them to achieve access to sensitive data of the company.
API server compromised by threat actors to compromise PowerReviews
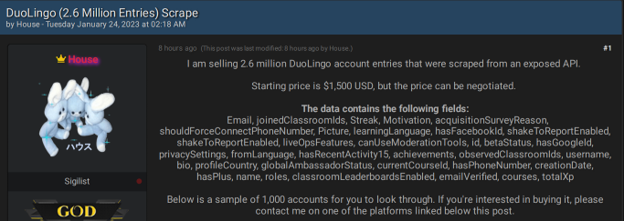
For sale: Duolingo database offered by an actor who obtained it through scraping an exposed API
How to Prevent?
- Strengthen Authentication and Authorization: Implement strong authentication mechanisms to verify the identity of API users.
- Secure API Keys: Use secure methods for storing and transmitting API keys.
- Input validation: Implement strong input validation to ensure that data sent to the API is in the expected format.
- Monitoring: monitor cybercrime sources to understand the interest of threat actors in API vulnerabilities and possible victims discussions.
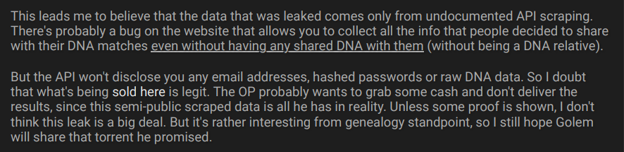
Threat actors discuss API flaws that led to 23andMe, a genetic profiling service leak
Cloud Storage Misconfigurations
As organizations increasingly depend on cloud services for diverse functions, securing their cloud-based infrastructure becomes a significant challenge. Cloud misconfiguration, encompassing gaps or errors, poses a risk by potentially exposing a business environment to security vulnerabilities.
KELA research has exposed how threat actors abuse cloud storage misconfigurations.
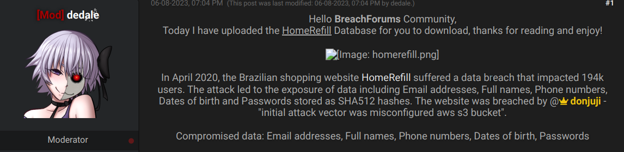
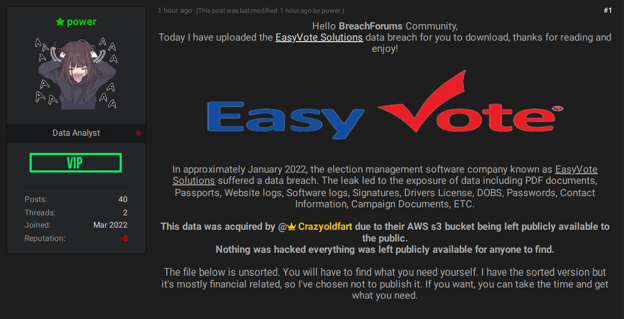
In June 2023, an actor shared a database of a supermarket in Brazil that exposed records of over 190,000 users. The actor claimed that the data was obtained by exploiting a misconfigured S3 bucket. S3, a service offered by Amazon Web Services (AWS), stands for Simple Storage Service. It enables users to store data and assets. S3 buckets, equipped with configuration options, pose a risk if set to be publicly accessible or if other misconfigurations exist, potentially granting unauthorized access to the stored data by threat.
Actor sharing a database that was compromised through misconfigured AWS S3 bucket
Actor has exploited AWS S3 bucket that was publicly available
How to Prevent?
- Data Encryption: Utilize encryption mechanisms provided by cloud service providers to protect sensitive information from unauthorized access.
- Identify Misconfigurations: Implement policies that help detect and pinpoint misconfigured S3 buckets that hold sensitive data.
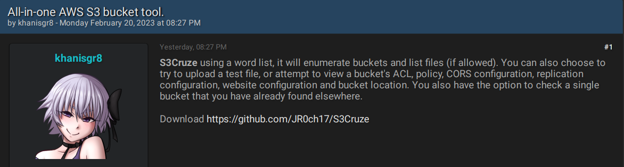
- Monitoring cybercrime sources: Track ongoing data breaches, cyber campaigns and tools that may exploit cloud storages.
Actor offering a tool to enumerate buckets and extract data
Third-parties Software Vulnerabilities
Third-party vulnerabilities refer to security vulnerabilities that arise from the use of external services or software. Organizations often rely on third-party vendors, partners, or applications to enhance their operations, yet they must ensure that these services are well protected.
One of the biggest data thefts of 2023 was executed by the Clop ransomware group abusing a zero-day exploit of Progress Software’s MOVEit Transfer. The attack impacted over 2000 organizations globally, resulting in data breaches for both MOVEit users and their customers.
KELA’s research reveals that threat actors frequently disclose vulnerabilities in companies’ third-party systems they exploit. In June 2023, the threat actor ‘dedale’ reposted a University of California database, mentioning that the 2020 data breach was made possible by a vulnerability in a third-party provider, Accellion’s, software. The Accellion file transfer application (FTA) data breach has impacted over 100 companies, with the. Clop ransomware identified as responsible for the attack.
Actor sharing a University of California database that was hacked by exploiting the “Accellion flaw”
In October 2022, the actor ‘thomaschweeizer’ shared a Unreal Engine Forum database, claiming that the forum had been compromised due to a SQL injection vulnerability in vBulletin. vBulletin, a proprietary Internet forum software package, uses a MariaDB or MySQL database server. The vBulletin SQL injection vulnerability enables attackers to execute malicious SQL statements effectively gaining control over a web application’s database server.
Unreal Engine experienced a data breach attributed to a SQL vulnerability
How to Prevent?
- Risk Assessment: Conduct risk assessments to identify and evaluate potential vulnerabilities associated with third-party relationships.
- Regular Security Audits: Conduct regular security audits of third-party systems, applications, and services. This ongoing monitoring helps identify and address vulnerabilities in a timely manner.
- Access Control Measures: Implement access controls and least privilege principles for third-party access. Only provide the minimum level of access necessary for the third party to fulfill their responsibilities.
Stealing or Obtaining Login Credentials to Database Services
Threat actors target login credentials for accessing applications and databases. These credentials may be acquired through attacks or a purchased on cybercrime markets. For example, an actor claimed to have compromised the Image Sharing website ClickASnap using leaked Amazon RDS credentials. Amazon RDS is a managed database service that supports several database engines.
Actor has obtained leaked Amazon credentials for gaining access to a photo-sharing platform
Actor saying he has obtained leaked credentials, which enabled him to breach Thai police
How to Prevent?
- Multi-Factor Authentication (MFA): Implement multi-factor authentication (MFA) to add an extra layer of security.
- Education and Awareness: Train employees on security best practices and raise awareness about the risks of phishing attacks.
- Monitoring cybercrime forums: cybercriminals buy stolen credentials on cybercrime forums. Therefore, it’s crucial to gain insights into threat actors’ activities on the cybercrime underground.
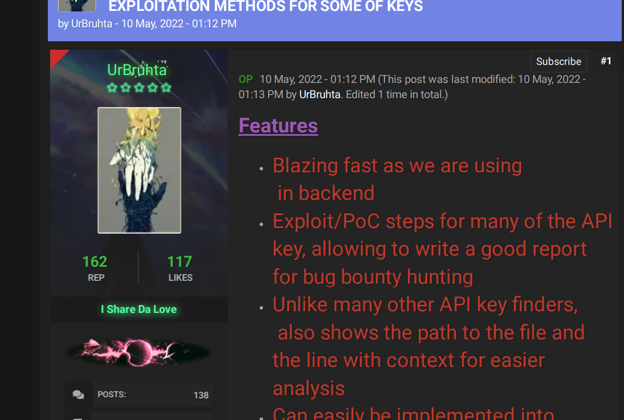
Actor providing details on acquiring API keys
Cybercriminals seek entry points to access corporate data through methods like injections, API vulnerabilities, misconfigurations, and third-party weaknesses. Another popular tactic is credentials theft. The disclosure of sensitive information can result in severe financial and reputational consequences, necessitating organizations to adopt protective measures against data leakage.
Empowering organizations with advanced visibility across various cybercrime sources, KELA’s cyber threat intelligence platform enables security teams to gain profound insights into the tactics, techniques, and procedures (TTPs) employed by threat actors. This understanding equips companies to effectively mitigate the risk of data breaches.
Take a proactive approach—experience the power of our platform with a free trial.