3 Minute Attribution of the ANTS Breach: Tracing “breach3d” Using KELA Intelligence and OSINT
3 Minute Attribution of the ANTS Breach: How KELA analysts attributed the ANTS breach — affecting ~12M French records — to a real-world individual in minutes, using threat intel and OSINT.
Published May 14, 2026

Background
In April 2026, the French National Agency for Secure Documents (ANTS) disclosed a cyber incident affecting its ants[.]gouv[.]fr portal after suspicious activity was detected between April 13-15. The breach disrupted online services for passports, national ID cards, driving licences, and residency documents, leading the agency to temporarily take application functions offline while investigations and remediation efforts were carried out. Shortly after disclosure, a threat actor operating under the moniker “breach3d” advertised a large ANTS dataset for sale on criminal forums, claiming it contained approximately 19 million records. French authorities, however, stated that the confirmed exposure currently affects around 12 million accounts, and the larger figure remains unverified.
According to ANTS and the French Interior Ministry, the exposed information likely included account identifiers and metadata, names, email addresses, dates of birth, and unique account IDs, while some records may also have contained postal addresses, places of birth, and phone numbers. The agency stated that biometric information, uploaded attachments, and passwords were not compromised, and that the leaked metadata could not directly be used to access accounts. Following the discovery, ANTS notified CNIL, ANSSI, and the Paris public prosecutor, with forensic and criminal investigations ongoing to determine the intrusion vector and the full scope of the breach.
In May 2026, French media reported that a teenager had been taken into temporary custody in connection with the incident, over suspected involvement in the breach and the alleged sale of the stolen data on dark web forums.
KELA's annual CyberCrime Report highlights that 10.7 million French compromised accounts were already identified in 2025, which ranks France 2nd among the most affected countries in Europe. The news further compounds the credential challenges facing Governments services across the globe.
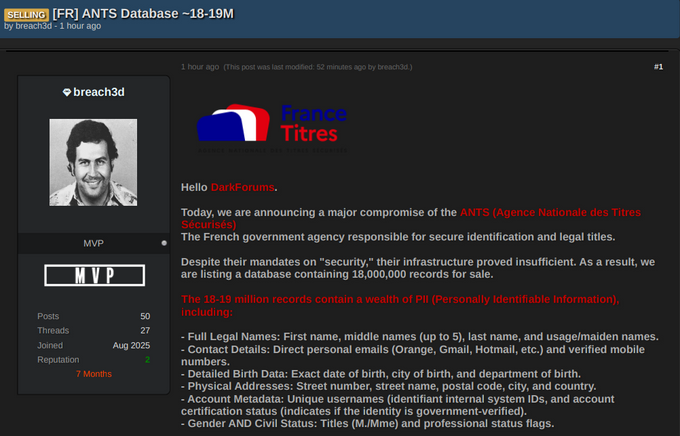
The actor’s ANTS post on DarkForums
breach3d Forum Activity
The breach3d actor registered on DarkForums in August 2025 and initially shared a session ID as a contact method. Early activity mainly involved commenting on breaches posted by others, likely to obtain or download the leaked material for personal use. These included cPanel access offers and credential lists. At one stage, the actor opened a service thread advertising “Custom Targeted Investigation Service,” offering OSINT investigations on request. Over time, the activity expanded to additional services, including offers for “private fresh logs,” likely referring to exclusive infostealer data.
After approximately four months of inactivity on DarkForums, the actor resurfaced and began publishing multiple fresh databases, starting with the French Ministry of Health, Police Nationale, and later the ANTS database. Following the ANTS leak, additional datasets were released, including material allegedly linked to the Peru National Police and Ministry of Transport, as well as documents originating from Brazil and other sources. In several breach posts, the actor claimed the intrusions were conducted together with “ExtaseHunters.” At this stage, it remains unclear whether ExtaseHunters refers to a separate partner, a group affiliation, or simply an alternate account controlled by the same actor.
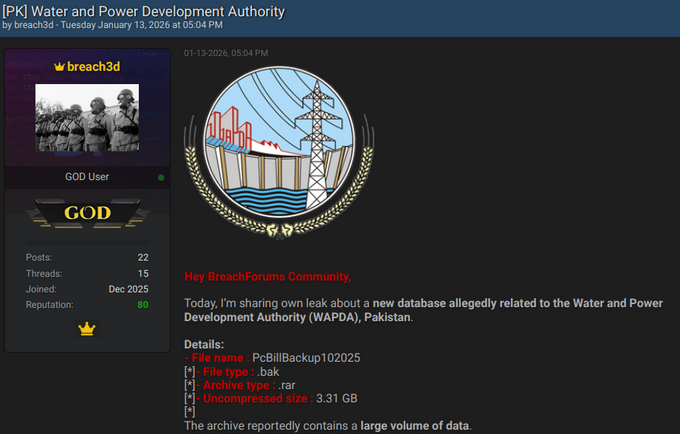
In addition, the actor was active on BreachForums, where the account was registered in December 2025. Similar to the activity observed on DarkForums, the actor primarily shared databases related to France, alongside additional datasets from Pakistan, Senegal, India, and Japan. The actor also claimed affiliation with the Lapsus$ hacking group and provided the Telegram handle @r00mc as a contact method.
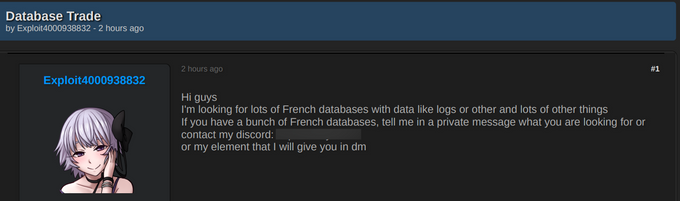
Using historical data from the available 10 year archive within KELA’s platform, KELA identified the actor’s previous username on DarkForums, used before adopting the “breach3d” moniker: “Exploit4000938832.” In September 2025, approximately one month after registering on the forum, the actor published a thread seeking database trade opportunities, stating that he was looking for large volumes of “French databases with data like logs or other and lots of other things.” The actor also allegedly offered for sale credentials related to Airbus internal systems, purported U.S. government logins, WhatsApp Reverse Engineering exploit, and several exploits he claimed to have discovered across multiple systems. Using this moniker, the actor shared additional identifiers in order to contact him like Telegram, Discord, and Matrix (“gohlcc”).
OSINT Traces
KELA has been tracking the actor’s activity and leveraged both KELA’s data lake and OSINT techniques to identify the individual behind the ANTS breach. One of the key breakthroughs came from multiple historical leaks affecting DarkForums over the past several years. Most notably, an April 2026 leak exposed users’ IP addresses across their forum activity. Using this data, KELA confirmed that the actor is based in France. Although some of the IP addresses associated with the account were linked to VPN services, several others resolved to French providers, including Orange Mobile and SFR. From a law enforcement perspective, this information alone could significantly assist in identifying the actor’s real identity.
By investigating the actor’s Discord username, KELA identified additional websites linked to the individual. The first is an OSINT related Intelligence service which offers multiple OSINT tools through various pricing plans. The actor’s Discord handle appears in the website’s partners section and is associated with “GOHLCC”, matching the actor’s Matrix username.
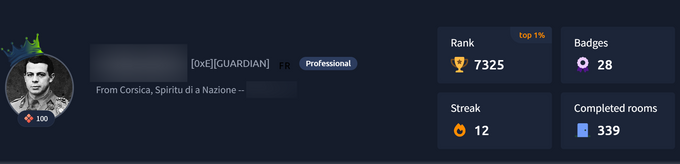
The second website appears to be a personal portfolio site, reportedly AI generated and hosted on GitHub, showcasing the actor’s cybersecurity background, skills, and projects. One of the projects was a WhatsApp Reverse Engineering exploit, just like he shared on DarkForums. On the portfolio website, the actor describes himself as an “independent cybersecurity player specializing in offensive and reverse engineering”, highlighting expertise in penetration testing, vulnerability exploitation, reverse engineering, and related fields. The site also references the actor’s personal values, including “ethics”. Most notably, the website contains what appears to be the actor’s full name, providing significant attribution intelligence. Searching for this specific full name yielded additional results, including more GitHub websites and profiles, a city in France (Corsica), a Gmail address, High ranking TryHackMe profile, Medium profile with two hacking blog posts, X profiles (@H4X0R1337_APT) mentioning “Gohlcc hacking group”, and a LinkedIn profile that also listed his age as 16.
The actor’s website and profiles from TryHackMe and GitHub
Bottom Line
Overall, the investigation demonstrates how a combination of KELA’s cybercrime intelligence coverage with historical underground forum data, and OSINT capabilities enabled rapid attribution of a high profile cyber incident to a likely real world individual. By correlating multiple data points, KELA was able to build a detailed profile of the actor behind the ANTS breach with relatively limited effort and without requiring access to classified or law enforcement only sources.