Will the REvil Story Finally be Over?
Published October 25, 2021.

According to recent reports, the operations of REvil ransomware were recently disrupted by a coordinated law enforcement operation (although not formally confirmed), taking their websites offline. Earlier that week, the most recently self-proclaimed representative of the RaaS bid farewells claiming that the servers were compromised – making it effectively the second time this year whereby the REvil (Sodinokibi) ransomware group has disappeared from radars.
Does it mean the gang’s story will end? And how will this affect other RaaS programs? KELA summarizes the group’s activities after the notorious Kaseya attack and assesses the possible consequences of its disappearance, considering the fact that ransomware affiliates became a driving power of RaaS (ransomware-as-a-service) operations.
Going Offline and Online
Following REvil’s July ransomware attacks on remote IT monitoring software provider Kaseya, the group’s representative (UNKN/Unknown) disappeared from the cybercrime forums, while sites maintained by the group – including the data leak, extortion, and payment portals – became inaccessible. Both security researchers and users of cybercrime forums wondered if the disappearance was related to a law enforcement operation or an exit scam.
Where is UNKN? Will the payments to REvil’s affiliates be made? Should the affiliates go into hiding in light of possible compromise of the REvil’s infrastructure? These were the questions discussed mainly on Russian-speaking forums and getting more reactions as soon as new information was published (for example, the fact that Kaseya received the master decryption key for their clients affected by the ransomware attack). The users remained without answers till September. Then, a user “REvil” (later renamed to 0_neday) who claimed to be a “coder” of the REvil ransomware took over the gang’s public activities.
Following REvil’s public infrastructure going back online, the new representative claimed the two-month absence was triggered by UNKN’s disappearance and the developers’ fear of being caught by law enforcement. According to the actor’s claims, the leakage of the master decryption key was allegedly caused by human error – i.e. including the universal key within one of the individual decryptor keys sent to the victims of the Kaseya attack that chose to pay the ransom. Finally, the new representative assured that the gang is in contact with all the affiliates and all payment issues would be resolved.
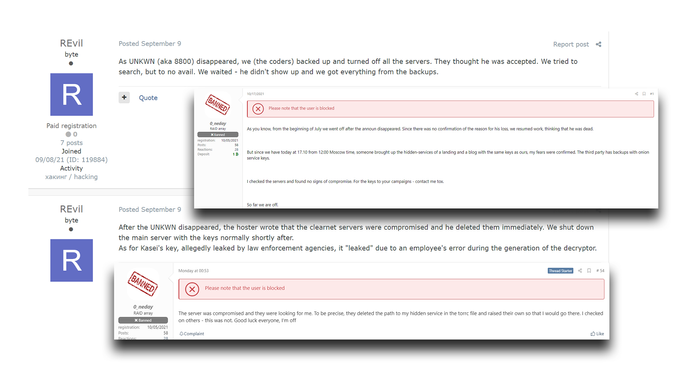
The first and the last messages of the recent REvil’s representative on Exploit and XSS forums
The following one month of activities was full of further speculations about UNKN’s fate, public clashes of the new representative with other threat actors, including LockBit’s administrator, the announcement of recruiting affiliates on RAMP, and publication of six new victims on REvil’s blog. The most common reaction between threat actors was the prejudice against working with REvil again since they did not provide sufficient explanations about the Kaseya attack, the group disappearance and re-emergence, and – probably the most serious claim – the reason behind using the same infrastructure that could be compromised. Combined with news about a secret backdoor enabling REvil’s creators to scam its affiliates, such discussions significantly disrupted REvil’s reputation.
The most careful actors were rewarded for their cautious behavior: on October 17, 2021, 0_neday announced on XSS that the group lost control over their Tor-based domains. The representative claimed that a third party compromised their Tor-based portal, deleted the path to his hidden service, and introduced a new path, probably in an attempt to identify this member. He claimed he is going offline, while later reports suggested the REvil operations were disrupted by a coordinated law enforcement operation.
Is it over though?
The disappearance of one RaaS will probably not influence the number or severity of ransomware attacks. Unfortunately, the RaaS business model is solid since affiliates can work with multiple operations. Even if the RaaS admins are arrested and the decryptors are published, it is very hard to trace affiliates and stop them as well. Moreover, many affiliates are working with different ransomware operations and will just move all the efforts to another RaaS once one of their partners is disrupted.
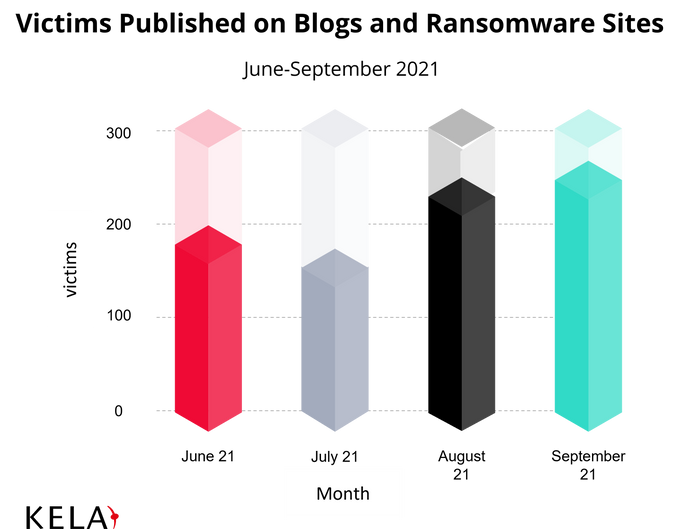
In June 2021, the last month of REvil’s full-time activities, 205 victims were published on ransomware blogs and data leak sites. Meanwhile, in August 2021, a full month after the group’s disappearance, 248 victims were published on the same platforms. Moreover, 251 victims were claimed in September 2021. Even when looking at this surface data (meaning the number of attacks that became public, while the actual number of ransomware victims is much higher), one can see that the ransomware groups’ activities are steadily growing. The disappearance of one group does not significantly influence the overall ransomware threat, as also could be seen from shutting down of DarkSide, Avaddon, and other groups active this year.
In the RaaS business model, the affiliates became the power equal to the developers of the ransomware strains and administrators of operations. While developers and administrators compete over the ransomware functionality and convenience of the affiliate panels, the affiliates are choosing targets, attacking them, and demanding ransom. Taking some servers offline is a way to disrupt the operation but it does not necessarily impose an actual cost to cybercriminals behind the operation – in this case, to affiliates and even ransomware operators (while it is still unknown what happened to UNKN, 0_neday appears to escape the cage, at least for now).
Therefore, consequences of a RaaS takedown, speculated as applied to the REvil case, may likely be the following:
- REvil’s developers and current administrators will lay low for some period of time and then will come back to the cybercrime scene, possibly using different identities. A second return under the same name and with the same product would appear to be the unlikely scenario though this decision fully depends on the balance between the gang’s members’ level of caution and a desire to earn more money. However, rebranding goes aligned with this group’s history which most likely includes evolution from GandCrab to REvil, changing their business model, and gaining new affiliates.
- REvil’s affiliates will continue to work with other RaaS operations, choosing the most attractive conditions and the most powerful malware strains. In the light of REvil’s infrastructure being compromised, some affiliates may adopt new identities as well.
- REvil’s competitors will choose targets more carefully, bypassing the government and critical infrastructure entities in an attempt to thwart unwanted attention from law enforcement. Possibly, other RaaS operations will introduce more safe interaction between the administrators and the affiliates, minimizing the risk of the affiliates getting caught in the case the core of the RaaS will be compromised – and vice versa.
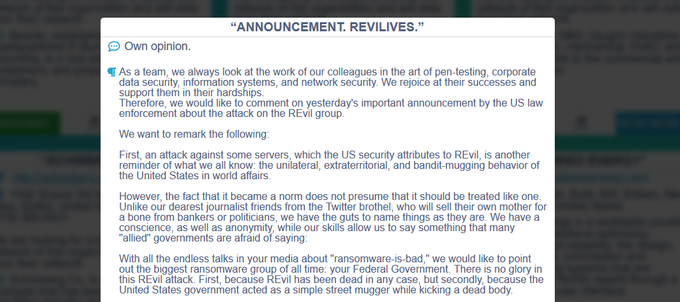
The reaction of the Conti ransomware gang to events around REvil
Despite the fact that REvil as a product quitting the cybercrime scene is a big accomplishment of whichever speculated law enforcement organizations, it is essential to remember that skilled cybercriminals who were cooperating with this RaaS are not going anywhere. They continue to search for new infection vectors, evolve their TTPs, and cooperate with more threat actors, thus requiring enterprise defenders to closely monitor their activities on cybercrime forums in order to proactively react to the threats.